by András Arányi The Access Control Trie (ACT) is an essential feature designed to manage access control in Swarm’s decentralized storage infrastructure. It enables publishers to grant or revoke access to specific content at the chunk level using encrypted session keys. This guide will walk you through the key concepts…

Introducing the Access Control Trie (ACT) in Swarm
by András Arányi
The Access Control Trie (ACT) is an essential feature designed to manage access control in Swarm’s decentralized storage infrastructure. It enables publishers to grant or revoke access to specific content at the chunk level using encrypted session keys. This guide will walk you through the key concepts and practical aspects of using ACT to protect your data in Swarm.
If you’re a content publisher and looking for a way to share data but maintain full control and privacy, you might find that the below concept of a fully fledged access control mechanism covers all your needs.
Content Publishers
⚠️ TLDR: Publishers can control access to their data by encrypting access keys for each viewer and adding/removing them from the ACT lookup table. ⚠️
As a publisher, you have full control over who can view your content. Using ACT, you can upload your data and grant access to specific grantees (viewers) by referring to their Swarm node wallets’ public keys. Additionally, you can revoke access at any time, ensuring that only authorized viewers have the ability to access your data.
What makes ACT unique is that, as opposed to other solutions which only encrypt data, ACT ensures that only the intended viewers will have access to the data. Everyone else is blocked, even from discovering an encrypted version of it. This significantly increases the privacy and security of your content, preventing unauthorized users from knowing the data even exists.
How to manage access:
- Upload your content to Swarm as you normally would, but with ACT request headers included.
- Assign access rights by adding the grantee’s public key to the ACT.
- If needed, revoke access by removing the grantee from the ACT.
Keep in mind: Publishers can control the latest version of content that grantees are able to access. If you update your content, viewers might still have access to an older version if they were granted access to that earlier version before.
You can learn more about how to manage access using tools like swarm-cli by following the tutorial in the Swarm documentation. These features are also fully supported by the Bee API (starting from version 7.0+), enabling any application to interact with them directly.
Grantees (Content Viewers)
⚠️ TLDR: Grantees can access the specific version of content that the publisher has granted access to, but may lose access to future versions if revoked. ⚠️
As a grantee, your ability to view the content is based on the public key of your Swarm node’s wallet and depends on the permission granted by the publisher. The process for gaining access is simple and secure, thanks to ACT’s encryption mechanisms.
How it works:
- Your Swarm node wallet’s public key is used as a session key, which is then used to create two additional keys:
- A lookup key to find your entry in the ACT lookup table.
- An access key decryption key, allowing you to decrypt the content access key specifically encrypted for you.
This ensures that only you can decrypt the content, and you can retrieve the version of the content you have (or have had) permission for.
How ACT Manages Grantee Access
ACT employs a sophisticated mechanism to manage grantee access using public-key cryptography and secure key derivation. At the heart of this system is the ACT lookup table, a key-value store that securely links each grantee’s Swarm node wallet’s public key to an encrypted access key. Here’s a breakdown of how it works:
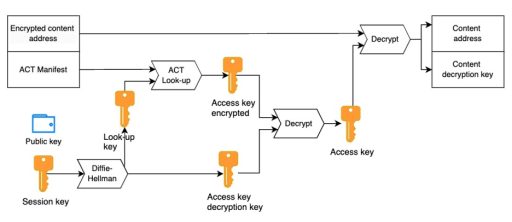
- Session Key:
Each grantee’s Swarm node’s public and private key pair serves as their unique session key. This session key is crucial because it forms the basis for all further encryption steps related to the grantee’s access. - Key Derivation via Diffie-Hellman:
Using Diffie-Hellman key derivation, the session key is used to derive two important keys:- Lookup Key: This key is used to identify the specific entry for a grantee in the ACT lookup table.
- Access Key Decryption Key: This key is used to decrypt the access key, which in turn allows the grantee to unlock the protected content.
- Encrypted Access Keys:
The content access key is encrypted specifically for each grantee using their derived decryption key. This ensures that only the intended grantee can decrypt the access key and thus view the content. This per-grantee encryption adds a layer of security, preventing unauthorized access even if someone else obtains the encrypted data. - ACT Lookup Table:
The lookup table itself is implemented as a key-value store within a Swarm manifest. Each grantee’s public key maps to an encrypted access key, ensuring that only authorized users with the correct session and decryption keys can retrieve the access key and, subsequently, the content. This table allows publishers to manage access dynamically, adding or removing grantees as needed without compromising the security of the stored content. - Adding and Removing Grantees:
Publishers have the flexibility to dynamically add or remove grantees from the lookup table. When a grantee is added, their public key and the corresponding encrypted access key are stored in the lookup table.
Version Control and Historical Access:
The ACT maintains a version history, which includes timestamps for each version of the access control list. If a grantee’s access is revoked for new versions of the content, they can still access older versions to which they had been granted permission, based on the relevant timestamps.
Encryption and Security in ACT
⚠️ TLDR: Every element in the ACT process is encrypted, ensuring complete security of content and access control. ⚠️
As demonstrated earlier, encryption is central to how ACT is implemented. Every component, from the grantee list to the content access keys, is encrypted using strong cryptographic methods. This ensures that only authorized users can access your data, and any tampering or unauthorized access is effectively prevented.
Here’s how encryption is applied:
- Grantee List Encryption:
The list of grantees is encrypted using the publisher’s lookup key, ensuring that unauthorized users cannot even detect the existence of the grantee list. This adds another layer of privacy, as only the publisher and authorized grantees are aware of who has access. - Access Key Encryption:
Each grantee’s access key is individually encrypted using their specific decryption key derived through the Diffie-Hellman process. This ensures that only the intended grantee can decrypt the access key and gain access to the protected content. - Historical Version Encryption:
All versions of the ACT, including older ones, are protected by encryption. This means that even if a grantee’s access is revoked, the historical data they had access to remains encrypted and secure.
Content Encryption:
Finally, the actual content itself is encrypted at the chunk level. Only those who possess the correct access key (which is encrypted for each grantee) can decrypt and retrieve the content.
Key Takeaways
- Publishers: Maintain control over your data and manage grantee access with fine-grained control using ACT. You can easily add or remove access rights and ensure your data is always protected by encryption.
- Grantees: Access specific versions of content securely, knowing that only you have the ability to decrypt the content you’ve been granted access to.
For anyone operating in the Swarm ecosystem, the Access Control Trie (ACT) represents a critical advancement in decentralized content management, offering robust security while maintaining flexibility in access control.
If you’re interested in learning more about how ACT works or how to implement it in your Swarm nodes, have a look at the Swarm documentation.
ACT opens up endless possibilities in new type of business applications on decentralised infrastructures. If you want to know how or you already have a concept in mind have a look at our article dedicated to this topic and register your interest in a consultation with us here

Swarm Mobile: Web3 Power in Your Pocket
Introduction: Digital Sovereignty Coming to Android
In a world where mobile devices act as the primary gateway to our digital lives, true digital sovereignty cannot exist if it is confined to desktop computers. At Solar Punk, we’ve observed a growing demand for privacy-focused mobile applications and a clear need for decentralized solutions that adopt a mobile-first approach.
But is it actually possible to connect to a decentralized storage network directly from a smartphone?
To answer this, we began experimenting with a Proof of Concept (PoC) to run a Swarm Bee node natively on Android. What started as an experiment has evolved into a concrete demonstration: the robust, censorship-resistant power of the Swarm network is fully capable of running right in your pocket.
Content Management with the Freedom of Mobile
We are proving that the same decentralized capabilities available on Swarm Desktop can be brought to a smartphone. By bridging a lightweight Go implementation (bee-lite) with a native Java interface for Android, we’ve created an app that doesn’t just connect to Swarm, but participates in it.
Current Features: A Node in Your Pocket
The Swarm Mobile app is designed to provide seamless access to the network without overwhelming your device’s resources. Here is what is already possible in the current Android implementation:
- Start Ultra-Light or Light Bee Nodes Automatically: Users can choose their level of network participation. The Ultra-Light mode provides a quick, resource-efficient way to download content from the network. For the real Web3 power—including uploading data and participating in network economics—the app automatically launches a Light node for you. The setup is managed behind the scenes; users only need to handle the initial wallet funding.
- Custom Gnosis RPC Configuration: Sovereignty means choice. Since the Bee node relies on the Gnosis chain for smart contract interactions, the app allows users to specify and connect to their preferred Gnosis chain RPC endpoint.
- Download from Swarm: Paste a Swarm Hash into the app, and the node will fetch and download the content directly to your device’s local storage.
- Create and Select Swarm Postage Stamps: To upload data, a Light Bee node needs a Postage Stamp. The app natively supports interacting with Swarm smart contracts to buy stamps (defining capacity and depth) directly from the mobile UI.
- Upload to Swarm: Select files from your Android device, pick an active postage stamp, and upload your data to the Swarm network, receiving the content’s Swarm Hash in return.
- Share Content with Swarm Hashes: Easily share your uploaded content with anyone, including Web2 users. The app’s Share functionality makes it simple to distribute your content address hash, enabling access without requiring others to run a node.
The Road Ahead: A Vision for the Future
Proving that a native Android Swarm node is viable is just the beginning. Our roadmap envisions transforming this foundation into a more complete mobile Web3 experience.
- In-App Node Funding: Currently, users have to fund their node from outside the app. Future iterations aim to support in-app funding, potentially leveraging existing solutions like the library powering the Swarm Multichain App, allowing users to top up directly from their phone.
- File Manager Integration: We plan to bring the intuitive, hierarchical folder-and-file experience of the Swarm Desktop File Manager to mobile, making decentralized data organization as simple as using Google Drive.
- Mobile Streaming: Imagine consuming decentralized multimedia streams on the go, or even broadcasting live video from your phone’s camera directly to the Swarm network.
- On-Device AI Assistants with ACT: This is where things get truly futuristic. A local AI model running on the device could use the Swarm node to store its “memory” and context. Combined with Swarm’s Access Control Trie (ACT), this setup would support private, user-controlled AI workflows.
- A Foundation for All dApps: Ultimately, this underlying native implementation can serve as the robust, privacy-focused decentralized storage layer for any mobile application seeking to break free from centralized cloud providers.
The future of the internet is decentralized, and it is increasingly mobile. We are incredibly excited to continue pushing the boundaries of what is possible on Swarm.
Ready to explore the code? Developers can dive into the native Android implementation and the bee-lite bindings over on our GitHub.Introducing the Access Control Trie (ACT) in Swarm

The Swarm File Manager: Bridging the Gap Between Web2 Comfort and Web3 Power
In our previous update, we introduced the concept of the Swarm File Manager: a radical layer of abstraction designed to make the unstoppable Swarm network as easy to use as a standard USB drive. Today, we are thrilled to announce that the vision is now a reality.
The release of the File Manager marks a pivotal moment for digital sovereignty. It translates the raw, censorship-resistant power of Web3 into the familiar comfort of traditional cloud storage, ensuring that true data ownership is within reach for everyone, without the steep learning curve.
Realizing The Vision of Digital Sovereignty
For years, the barrier to entry for decentralized storage has been technical complexity. Storing a file on Swarm previously required understanding Postage Stamps, calculating depth and amount, managing batches, and handling content hashes. While these primitives ensure the network’s resilience, they are alien concepts to the average user who simply wants to safekeep their photos or documents.
The Swarm File Manager solves this by abstracting cryptography and economics behind a familiar interface. We have built a bridge where users interact with “Files” and “Drives,” while the software manages the immutable chunks and decentralized incentives in the background.
Now Live: What the File Manager Can Do
The File Manager is built around simplicity and control. Here is a deep dive into the features available in this release:
1. The “Drive” Concept
We have replaced the complex management of postage stamps with the intuitive concept of a Drive, which not only simplifies the process but also proactively notifies you when a drive is nearing expiration.
- Customizable Storage: Users can create and upgrade Drives with specific capacity and validity periods (Time-to-Live). We have also introduced a “Security Level” setting, leveraging Swarm’s erasure coding feature. This allows you to define the redundancy of your data, ensuring it remains retrievable even if parts of the network go offline—a level of durability that goes far beyond standard replication.
- Automated Economics: When you create a Drive, the File Manager automatically calculates and purchases the necessary underlying postage batch. You don’t need to do the math; you just decide how much space you need.
- Admin Drives: These special drives add advanced file management capabilities by storing additional metadata, effectively acting as your personal catalog on the Swarm network.
2. Seamless Management
Managing decentralized assets should not feel like managing a database.
- Smart Drag-and-Drop: Uploading files is as simple as dragging them from your desktop into the browser. The interface now features a visual progress window that tracks every upload and download in real-time, giving you clear feedback on the status of your transfers, whether it’s a single document or a batch of photos.
- Renaming & Versioning: Mistakes happen. The File Manager allows you to rename files effortlessly. More importantly, it supports Version History, allowing you to inspect or restore past snapshots of a file—a crucial feature for collaborative work and data integrity.
- Deep File Inspection: For users who need more detail, the new “Get Info” functionality provides a comprehensive view of any file’s metadata. You can instantly inspect file size, type, creation dates, and even copy the raw Swarm Content Hash—bridging the gap between a user-friendly UI and the underlying protocol.
3. Organizational Tools
As your decentralized library grows, staying organized is key.
- High-Speed Search: Find files instantly by name or type across all your drives.
- Smart Sorting: Organize your view by name, size, or date modified to stay on top of your data.
- Advanced Filtering: Narrow down your view by scope (specific drive vs. all drives) or status (active vs. trash).
4. The Deletion Hierarchy
Decentralized storage is often immutable, but your interface shouldn’t be cluttered. We introduced a three-tier deletion system:
- Trash: A “soft delete” that moves items out of sight but keeps them recoverable.
- Forget: Removes the local reference to the file, decluttering your view while the data persists on the network until it expires.
- Destroy: The permanent removal of a Drive (and its underlying postage batch), rendering the data inaccessible.
The Roadmap: The Future of Hierarchy
While the current release introduces a robust flat-file system, we are already building the next evolution of organization: Deep Hierarchy.
In upcoming releases, we will move from a file list to a fully hierarchical folder system.
- Folder Uploads & Creation: You will be able to drag and drop entire directory structures from your OS, or create new folders directly in the UI, and the File Manager will preserve the nesting on Swarm.
- Deep Navigation: Navigate in and out of subfolders just like you would in a desktop file explorer.
- Drag-and-Drop Organization: Move files into folders and reorganize your directory structure on the fly.
- Folder Insights: Specialized “Get Info” modals will provide statistics for entire directories, not just single files.
Expanding the Ecosystem: Multichain Funding
Finally, we recognize that acquiring the specific utility token (xBZZ) to fund storage can be a friction point for new users. To solve this, we are developing a Multichain Support plugin for Swarm Desktop.
This future update will allow users to fund their File Manager storage directly from their connected wallet across different chains. By making the “fuel” for decentralized storage borderless, we are ensuring that Swarm becomes the universal hard drive for the Web3 ecosystem.
Ready to take control of your data?
Download the latest version of Swarm Desktop today and experience the future of file management: decentralized, private, and undeniably yours.

The Evolution of Streaming on Swarm: Introducing MSRS
Earlier this year, we took a significant step forward in decentralized multimedia with the release of our open-source multimedia libraries and the launch of the Multimedia Streaming Social Demo (MSSD). The MSSD was a proof of concept that demonstrated the power of live streaming on Swarm, showcasing a future free from censorship and centralized control. The response was incredible, and it confirmed our belief that the world is ready for a new paradigm in media delivery.Today, we are thrilled to announce the next evolution in that journey: the Multimedia Streaming Restricted Solution (MSRS).
From Demo to Dynamic Solution
While the MSSD was a powerful demonstration, the MSRS is a robust, feature-rich application designed for real-world use. It’s a B2B solution that empowers our partners to build their own decentralized streaming services on top of Swarm. We’ve taken the core concepts of the MSSD and rebuilt them with scalability, security, and partner needs at the forefront.
What’s New in MSRS?
The MSRS is more than just an update; it’s a complete rethinking of what a decentralized streaming architecture can be. Here are some of the key features that set it apart:
- Advanced Stream Management: Partners now have access to a powerful admin interface. They can pre-configure and schedule streams for a future date and time, complete with a title, description, and a custom thumbnail. This allows for professional event setup and promotion well in advance.
- Partner-Controlled Stamp Management: A crucial step toward self-sustainability, MSRS gives partners direct access to a “Swarm Stamp Manager”. Through this interface, they can monitor the status and Time-to-Live (TTL) of the postage stamps used for their streams and top them up to ensure their content stays online. This serves as a powerful demonstration of how future applications could enable individual users to manage their own content persistence on Swarm.
- Engaging Live Chat: The viewer experience has been significantly upgraded with a new chat interface. Viewers can now interact with streams and each other using emoji reactions and threaded conversations, fostering a more dynamic and engaging community experience.
Waku Integration: We’ve integrated the Waku protocol for real-time signaling. This reduces latency and improves the overall user experience by eliminating the need for constant status polling.
Under the Hood: A Scalable, Multi-Tenant B2B Architecture
Core Architectural Principles
The system is built on a clustered, multi-tenant infrastructure, a core design choice that guarantees high availability and seamless horizontal scaling. This architecture ensures that each partner’s data and streaming environments are completely isolated and protected within the ecosystem. As new partners are onboarded, the infrastructure can scale effortlessly to meet growing demand without compromising performance or security.
DevOps and Infrastructure Management
We have developed a suite of proprietary scripts, actions, and utilities for streamlined infrastructure management. This custom tooling provides the flexibility to provision, configure, and manage the entire platform—or its individual components—with precision. This version-controlled approach to infrastructure allows for granular control over each partner’s instance, ensuring stability, consistency, and rapid deployment cycles.
System Components
An MSRS instance is composed of four primary, decoupled components:
- Ingestion & Transcoding Service: A dedicated Node.js service responsible for ingesting RTMP streams. Upon receipt, it efficiently transcodes and uploads the content to the Swarm infrastructure.
- Stream Aggregator: This service acts as a handler for application-level stream data. Accessible via GSOC, it manages real-time data changes within Swarm, such as updates to the master stream list and metadata.
- Chat Aggregator: Functioning similarly to the Stream Aggregator, this GSOC-accessible service manages the real-time lifecycle of live chat functionalities associated with each stream, ensuring reliable, low-latency communication.
Client Application: The front end is a sophisticated Single Page Application (SPA) that provides the primary user interface. Evolving from its predecessor (MSSD), the client offers a rich user experience for stream viewing and live chat. Integrated within the client, this version provides robust administrative capabilities. It leverages a simple, Swarm-based authentication mechanism to grant authorized users access to advanced features, including comprehensive stream management (create, edit, delete), metadata enrichment, content pinning, and simple stamp management.
The Future is Decentralized
The release of MSRS is a major milestone in our mission to build a more open and equitable internet. We believe that decentralized technologies like Swarm are the future of media, and we are committed to providing the tools and infrastructure that will make that future a reality.
With MSRS, we are not just offering a product; we are inviting you to be part of a movement. A movement to reclaim our data, our content, and our digital sovereignty. A movement to build a better internet for everyone.
Get Involved
Are you a developer, creator or brand shaping the next wave of streaming? Connect with us to discover MSRS and see how you can join the decentralized media revolution!
To learn more ,join our side event in Buenos Aires during Devconnect, where you can meet the team and explore the future of decentralized media firsthand.
The future is bright, and it’s being built on Swarm. Come build it with us!
The Swarm File Manager: Bringing Cloud Storage Usability to Decentralized Storage
Swarm is the resilient, censorship-resistant, decentralized storage and communication layer of Web3. Its core strength lies in its layered design: the interwoven systems of Postage Stamps, Feeds, Chunking, and Incentives that ensure data persistence and integrity without reliance on any central server.
However, complexity is the enemy of adoption. To unlock Swarm’s full potential for a broad audience, it needed a radical layer of abstraction. This is exactly what the new File Manager adds to Swarm Desktop. It replaces daunting technical concepts with a familiar, intuitive user experience, delivering the convenience users expect from cloud storage services, while leveraging the resilience and security of the Swarm protocol.
Here is a breakdown of how the File Manager transforms raw Swarm power into features everyone can use.
Abstracting the Economics: From Stamps to “Drives”
At the heart of Swarm’s persistence model are Postage Stamps, which prove a user has paid for their data to be stored over time. Managing these previously required understanding concepts like depth and amount.
The File Manager replaces this complexity with the simple concept of a Drive.
- Drives as Storage Containers: A “Drive” is a user-friendly abstraction of one or more Postage Stamp batches. Users can create multiple drives (e.g., “Work,” “Personal”) just like setting up partitions on a physical computer.
- Capacity and Expiration (TTL): Instead of the need of calculating a depth and an amount, users now specify familiar parameters: Initial Capacity (in GB) and Desired Lifetime (in months/years). Users also select a Security Level, which determines the level of erasure coding applied to their data for increased fault tolerance. The File Manager automatically translates these human-readable inputs into the correct Swarm stamp batch configurations, managing the underlying BZZ token expenditure and gas fees paid in xDAI.
- Simplified Maintenance: If a drive is “Low Capacity” or “Expiring Soon,” users are immediately notified with simple “Upgrade” buttons to Extend Lifetime (top-up the stamp) or Increase Capacity (increase the stamp’s depth).
Enabling Mutability: Version History and Renaming
Swarm is fundamentally immutable; once data is uploaded, it is split into chunks and each piece is addressed by its content. That means every change creates a new version, while the original remains unchanged. But cloud storage users expect to rename, edit, and move files. The File Manager enables this by wrapping Swarm’s core mechanisms in user-friendly features:
- Version History: Every time you upload a file with the same name, the File Manager doesn’t overwrite the old data. Instead, it creates a new file version. This is tracked using Feeds, which is essentially a chronological log (built on Single Owner Chunks (SOCs)) pointing to the address of the latest file content. The Version History feature instantly exposes this audit trail, allowing users to inspect, download, or Restore any past snapshot.
Metadata-Only Renames: If you rename a file, the manager simply records a new entry in the underlying metadata feed. Since the content itself hasn’t changed, no new data is uploaded to Swarm, making the operation instantaneous and cost-efficient—a huge advantage over cloud storage services, some of which might duplicate files upon renaming.
Granular Deletion and the ‘Trash’ Concept
Deletion in decentralized storage is philosophically complex. Since data can propagate across many nodes, immediate, global deletion is impossible and undesirable (however, this functionality may be introduced with a future Swarm feature, the DREAM protocol). The File Manager offers a powerful, three-tiered deletion system grounded in Swarm’s architecture:

This gives the user precise control, from a soft “Recycle Bin” deletion to permanent stamp removal.
Seamless User Experience and Scalability
Beyond core functions, the File Manager delivers a suite of essential UX features that make decentralized storage feel modern:
- Multi-Drive Navigation: A familiar sidebar tree view allows quick switching between different Drives, while the Trash view aggregates deleted items grouped by their original location.
- Unified Search: A quick search bar allows users to find files instantly across all active Drives and the Trash, much like a desktop operating system search tool.
Asynchronous Status: Complex, time-consuming operations (like creating a new stamp/Drive or bulk uploading large files) are treated as Asynchronous Operations and tracked with progress bars, notifications, and toasts to keep users informed.
What’s Next?
The File Manager was presented at the latest Swarm Community Call (recording available here) and is expected to be released officially as part of Swarm Desktop in October.
Looking ahead, the Solar Punk team is actively working on introducing fine-grained permissions for your decentralized data, by extending the File Manager with Access Control Trie (ACT) functionality (read more). It will allow users to grant or revoke access to individual files on their Drives, marking the next major step toward a comprehensive, permissioned decentralized storage platform.
In essence, the Swarm File Manager serves as the crucial application layer that translates complex economic and cryptographic primitives—Postage Stamps, Erasure Codes, Single Owner Chunks, and Feeds—into the intuitive file management interface users expect. It is the bridge that takes Swarm from a cutting-edge protocol to an adoption-ready platform.

From Universal Adapters to Decentralized Minds: The MCP Revolution
We should strive for a future where AI evolves not as a monolithic power in the hands of a few, but as a vibrant, decentralized ecosystem nurtured by many. We argued that this future is not only possible, but is actively being built on Swarm. That vision is no longer on the horizon, it’s here and gaining real-world momentum. Recent analysis from firms like Gartner and Forrester shows a significant uptake, with a majority of organizations already utilizing MCP to enhance their AI applications.
The catalyst for this revolution is the Model Context Protocol (MCP): a universal standard that allows any AI agent to connect to any tool, API, or data source. This simple, powerful idea eliminates the need for brittle, one-off integrations, paving the way for a truly interoperable network of intelligent agents.
What started as a promising concept is now a practical reality. The MCP isn’t just being tested, it’s being deployed by some of the biggest names in the development world, proving its power and utility at scale. This trend is accelerating, with Gartner projecting that by 2026, 75% of API gateway vendors will incorporate MCP features.
This shift signals the beginning of a new, agentic era of computing. And the Swarm MCP is ready to carry this revolution to its logical conclusion: a truly decentralized, unstoppable ecosystem.
The Tipping Point: GitHub and the Rise of the Hosted MCP Server
For years, the dream of the AI-powered developer has been hampered by friction. Running agents locally meant wrestling with Docker containers, rotating personal access tokens, and manually pulling updates. It worked, but it was a hassle. That era is officially over.
The clearest signal of this new wave is the rapid development and adoption of hosted MCP servers, and the premier example is the GitHub MCP server.
With its managed MCP endpoint, GitHub has transformed Copilot from a brilliant autocompleter into a genuine AI assistant capable of executing complex development workflows. The game has fundamentally changed. Gone are the days of infrastructure headaches. Now, with a simple, one-time OAuth authentication, developers gain access to a persistent, always-up-to-date suite of tools.
Want to automate the creation of a pull request, triage a security alert, or debug a failing CI/CD pipeline? You can now do it all from a simple chat prompt.
This is more than just a convenience, it’s a paradigm shift. GitHub’s implementation demonstrates the core promise of the MCP standard: when you give AI agents a universal language to interact with tools, you don’t just improve existing workflows, you invent entirely new ones. Their roadmap, which includes features like assigning issues directly to Copilot agents, points to a future of seamless agent-to-agent collaboration.
While GitHub’s server runs within a centralized platform, it serves as a powerful proof-of-concept for the MCP model, showing that the ‘universal adapter’ concept is not just theoretical, it’s practical and transformative.
The Swarm MCP: Bringing the Revolution to the Decentralized World
The success of the GitHub MCP server is a watershed moment. It proves the power of the protocol. But it also presents a new danger: that the open, interoperable future of AI will simply be re-centralized on a new set of proprietary platforms.
While GitHub validates the model, Swarm provides the truly decentralized foundation necessary to ensure this revolution benefits everyone. It delivers what centralized architecture simply can’t: persistent, censorship-resistant memory for agents, and true, cryptographically secured data sovereignty for users and their AI counterparts.
And the bridge is already built. The Swarm MCP Proof of Concept (POC) was a resounding success, proving its viability across multiple MCP-capable clients and core AI models.
The POC demonstrated that an agent, with no special configuration, can easily:
- Upload and retrieve files, folders, and text directly on Swarm.
- Use Swarm Feeds as a reliable, tamper-proof memory log.
- Share data and context with other agents simply by passing a Swarm reference.
The foundation has been laid. The proof is in the code. A home for AI agents is being built on Swarm.
What’s Next: From a Working POC to a Robust MVP
Building on the POC’s success, work is already underway to evolve the Swarm MCP into a production-ready MVP. The goal is to make using Swarm feel like a native utility for any AI agent. Our focus is on delivering a robust and developer-friendly solution with streamlined storage handling, enhanced security for agent communications, and effortless integration into popular AI frameworks.
Build the Future With Us
A new paradigm for AI is here. The Model Context Protocol is the universal language that will allow intelligent agents to collaborate at a global scale. GitHub is proving its incredible power and efficiency in the world of software development. The Swarm MCP is taking that power and unleashing it on a decentralized, resilient, and open foundation.
This is the Solar Punk vision in action: a vibrant, self-sustaining digital ecosystem where AI agents, owned by their creators and communities, can collaborate to solve real-world problems.
The future of AI is being built today. Let’s build it together.
- For Developers: Dive into the Swarm MCP on GitHub. Explore the code, try it out with an MCP-capable client and your favorite LLM, and help us forge the infrastructure for a decentralized world.
- For Dreamers and Builders: Join the conversation on the Swarm Discord. Share your ideas, challenge our assumptions, and be a part of the community that’s making this future a reality.

From IPFS to Swarm: Your Bridge to a Truly Decentralized Web
The path to a truly decentralized future often involves untangling ourselves from the lingering threads of centralized systems. At Solar Punk, we’re dedicated to forging the foundational infrastructure for censorship-resistant platforms and genuinely sovereign applications on Swarm.
That’s why we’re thrilled to announce a major step forward for developers and businesses ready to fully embrace the decentralized web: the unveiling of our new ipfs-to-swarm GitHub repository!This open-source TypeScript CLI tool isn’t just a piece of software. It’s a comprehensive toolkit and guide designed to help you seamlessly migrate your data from IPFS to Swarm.
Why Swarm is the Future of Decentralized Storage
You might be asking, “Why migrate?” While IPFS is a valuable decentralized protocol, Swarm takes the promise of Web3 a giant leap further by providing an incentivized data layer. This means Swarm offers several compelling advantages for building truly unstoppable applications:
- Guaranteed Data Availability: Unlike IPFS, which relies on external pinning services, Swarm includes a native bandwidth market and built-in economic incentives that ensure your content stays available.
- Superior Performance: Swarm uses smaller 4 KB chunks, allowing for more efficient storage and faster retrieval, even for rarely accessed files.
- Unwavering Censorship Resistance: Content on Swarm is nearly impossible to remove, protecting against both internal and external pressure. This supports permissionless publishing and ensures data remains accessible beyond the control of any single entity.
- Enhanced Privacy and Access Control: Swarm offers strong privacy features, built-in encryption and, crucially, Access Control Trie (ACT) permissions. ACT, a key Solar Punk contribution, gives you granular, cryptographically secure control over who can access your data, opening doors for private sharing, content monetization, and secure decentralized platforms.
- Integrated Incentives: Swarm’s native BZZ token rewards users who contribute storage resources, fostering a self-sustaining network.
Solar Punk is at the forefront of building on Swarm, making it easier than ever for developers to create robust, censorship-resistant applications.
Your Migration Bridge
The ipfs-to-swarm repository makes the transition from IPFS to Swarm straightforward and efficient. This TypeScript CLI tool performs the core migration steps: downloading content from IPFS and then re-uploading it to the Swarm network.
What the Tool Offers:
- Single File Migration: Easily migrate individual files by providing their IPFS Content Identifier (CID) and your Swarm postage batch ID.
- Bulk Migration: For those with extensive data, the tool can download all files and directories from your IPFS MFS (Mutable File System) root directory, preserving the original structure as it uploads them to Swarm.
- Prerequisites and Setup Guidance: The repository includes clear instructions on setting up your infrastructure, including running a Bee node, using postage stamps, and configuring your IPFS node.
- Stamp Management Insights: Learn how to estimate the required postage stamp capacity, purchase stamps, and monitor their validity and usage to ensure long-term storage.
The tool automates chunking, cryptographic hashing, and distribution of your data across Swarm’s network of nodes, ensuring its resilience.
Building the Unstoppable Future, Together
At Solar Punk, we believe in giving you the tools to take control of your digital destiny. The ipfs-to-swarm repository is part of our commitment to making decentralized infrastructure both accessible and powerful. It’s an essential step towards enabling self-sustaining, decentralized, and unstoppable communities.
Are you ready to unleash true data ownership and user control?
Explore the GitHub repository: https://github.com/Solar-Punk-Ltd/ipfs-to-swarm.
If you have a large-scale migration in mind, or your data model is complex and you need assistance in structuring your data on Swarm, don’t hesitate to reach out to Solar Punk for professional consulting. We’re here to help guide your journey into the decentralized future!

The Future of AI is Decentralized, and It’s Being Built on Swarm
We stand at a crossroads. Artificial Intelligence is evolving at a breathtaking pace, but its immense power is becoming concentrated in the hands of a few giant corporations. This path leads to a future of data silos, central points of failure, and a world where we don’t truly own the tools that shape our lives.
But what if we chose a different path? Imagine a future where AI is not a product owned by a few, but an ecosystem nurtured by many. A world where networks of independent, collaborative AI agents work together to solve humanity’s challenges—owned and operated by their creators and communities. This isn’t just a distant dream. This is the Solar Punk vision for AI, and its foundations are being laid today through a groundbreaking project: the Swarm Model Context Protocol (MCP).
What is the MCP? The Universal Adapter for AI
To build a decentralized AI ecosystem, we first need a common language. Think of the Model Context Protocol (MCP) as a universal adapter—like a “USB-C port for AI.” It’s an open standard that lets any AI agent connect to any external tool or data source without needing custom-built, one-off integrations.
This simple but powerful concept unlocks a world of possibilities. It allows developers to create a vibrant, interoperable ecosystem where agents can discover and use any tool, fostering innovation and collaboration on a massive scale.
Why Swarm? Building on a Resilient Foundation
If MCP is the common language, Swarm is the ideal platform to build it on. Its decentralized storage and communication infrastructure is tailor-made for AI, offering:
- True Decentralization: As a peer-to-peer network, Swarm has no central point of control. Data is distributed globally, making it resilient to censorship and single points of failure. AI agents built on Swarm operate freely and autonomously.
- Persistent Memory: AI agents need somewhere to store their “memories”—their knowledge, logs, and experiences. Swarm provides a permanent, immutable, and reliable home for this critical data.
Data Sovereignty: In the age of AI, data ownership is paramount. Swarm gives users and agents full control over their own data. This is supercharged by tools like the Access Control Trie (ACT), which enables fine-grained, cryptographically secure control over who can access data, paving the way for everything from private collaboration to monetized AI models with provable provenance.
From Theory to Reality: The Proof of Concept is a Success
This vision isn’t theoretical anymore. A recently completed Proof of Concept (POC) demonstrates that the Swarm MCP can act as a seamless bridge between AI agents and the Swarm network.
The POC proved that an AI agent can easily:
- Upload and retrieve text, files, and even entire folders on Swarm.
- Use Swarm Feeds as a persistent memory log.
- Share data with other agents by simply passing a Swarm reference.
The bridge is built. The concept works.
The Road Ahead: Nurturing a Digital Ecosystem
This successful POC is just the first step. In a joint effort, the Swarm Foundation and Solar Punk are now charting a course for what comes next. Guided by shared principles, the roadmap isn’t just about code; it’s about nurturing a complete, self-sustaining digital ecosystem on Swarm. The key directions include:
- Strengthening the Foundation: Evolving the Swarm MCP into a robust, production-ready solution that is easy for any developer to integrate into popular AI frameworks.
- Fostering Collaboration: Creating the pathways for a true community of agents. This means building a decentralized registry on Swarm so agents can discover each other, and enabling them to communicate directly and securely without intermediaries.
Building a Thriving Economy: Designing the framework for a vibrant marketplace where agents can be compensated for their work. This includes systems for posting tasks, bidding on jobs, and building on-chain reputation to foster a web of trust.
Join Us in Building the Future
The Swarm MCP is more than a technical project; it’s a cornerstone for a more open, resilient, and collaborative digital world. It’s a bet on a future where the power of AI is accessible to all, not just a select few.
We invite you to be a part of it:
- Developers: Explore the Swarm MCP project on GitHub.
- Dreamers and Builders: Join the conversation on the Swarm Discord.
Let’s build a brighter, decentralized future together—one unstoppable AI agent at a time.

Building the Unstoppable Web: Inspired by BitChat and the Power of Peer-to-Peer
The recent unveiling of Jack Dorsey’s BitChat is an exciting development in the quest for truly sovereign digital communication. Its core ethos of peer-to-peer, censorship-resistant messaging resonates deeply with our mission. While BitChat explores what’s possible using Bluetooth mesh networks, we at Solar Punk are building the tools for this unstoppable future on an even broader scale, using the robust decentralized infrastructure of Swarm.
Swarm is a peer-to-peer network of nodes that provides censorship-resistant decentralized storage and communication, aiming to be the operating system for a re-decentralized internet. It’s not just about moving data; it’s about empowering users with permissionless publication and true data ownership. Honored with a Swarm Foundation Fellowship, Solar Punk is developing libraries that make building on this powerful foundation more accessible.
Here’s a look at the tools we’ve created to make the decentralized web a reality:
Access Control Trie (ACT): Your Data, Your Rules
A key contribution from Solar Punk is the Access Control Trie (ACT), an advanced encryption and key management system now integrated into the Swarm protocol. ACT gives content publishers precise, granular control over who can access their data, unlocking essential use cases for individuals and businesses:
- Secure Content Delivery: Manage subscription-based content without relying on a central server.
- Private Data Sharing: Safely share sensitive information, from AI training models to personal health records, with provable provenance and full user control.
- Decentralized Social Networks: Build private communities where access can be granted or revoked on your terms.
Decentralized Multimedia Libraries: Unstoppable Communication
We have released the first version of our Multimedia Middleware libraries to fast-track the development of decentralized social and media applications on Swarm. These libraries provide cost-effective and scalable building blocks for censorship-resistant platforms, enabling features like:
For businesses, this means faster deployment and lower development costs when creating the next generation of social networks, streaming services, or metaverse experiences.
Devcon.buzz: A Blueprint for Privacy-Focused Apps
To showcase the above capabilities, we built Devcon.buzz for Devcon7 in Bangkok. Running entirely on Swarm, the app provided a privacy-focused platform for attendees to connect and share ideas. It demonstrated:
- Decentralized commenting using Swarm’s Graffiti feeds
- Group chat spaces and private, user-owned notes
- The entire Devcon agenda loaded directly from Swarm
Toward a Truly Decentralized Web
The vision of a mesh network independent of traditional internet infrastructure is deeply embedded in Swarm’s DNA. As a peer-to-peer network, Swarm distributes data across a global network of nodes, making it resilient to failures or interference. Its core design, from Forwarding-Kademlia routing to content-addressing, lays the groundwork for a network that can function and thrive even without centralized internet infrastructure. The ability to run local nodes and access Swarm content directly, as demonstrated by Devcon.buzz, marks a crucial step toward this vision.
The rise of projects like BitChat reinforces our belief that the future is decentralized. At Solar Punk, we’re not just watching this future unfold—we’re actively building it on Swarm.
Are you ready to join us in shaping a brighter, decentralized tomorrow?

The Price of Permanence: Comparing Swarm and Arweave
Storing data securely is essential for the decentralized internet. To meet this need, Arweave and Swarm both aim to provide a storage layer free from censorship, gatekeepers, and centralized control. Each system incentivizes node operators to store data reliably while keeping costs low enough to remain accessible, and high enough to keep the system self-sustaining. It’s a careful balancing act with different approaches. This article compares the basic economics, incentives, and long-term risks of both systems.
Let’s begin with a general comparison:
| Arweave | Swarm | |
| Payment model | One-time, fixed | Top-up balances via postage stamps |
| Blockchain | Arweave (native) | Built on Ethereum (Gnosis Chain) |
| Token | AR | BZZ |
| Token Atomic Unit | Winston | PLUR |
| Risks/ Assumptions | Kryder’s Law, AR token value | Ethereum ecosystem, active nodes |
| Economics | Proof-of-Work, Storage Endowment | Redistribution Game |
| Live Network Health | ViewBlock | Swarm Scan |
| Live Fees | Arweave fees | Swarm fees |
Arweave offers a simple promise to users: “pay once, store forever.” The price paid when uploading a new piece of data guarantees storage for at least 200 years. There is only one transaction, and the time horizon is fixed for all users.
Swarm’s system is more flexible and adaptable. It allows users to choose how long their data stays available, based on how much they fund their storage. Uploaders purchase batches of postage stamps. A batch represents a quota (e.g. 20GB), which entitles the owner to issue and assign a postage stamp to a number of chunks needed to store that data. The batch also acts as a wallet from which the storage rent is automatically deducted. The balance decreases over time, and the data remains available until the funds run out.
Arweave’s Storage Endowment
“Arweave draws inspiration from Bitcoin’s proof-of-work structure for achieving consensus and adapts its implementation to incentivize the permanent storage of information within its network.” – Arweave lightpaper
Like Bitcoin, Arweave runs its own blockchain. Miners store and retrieve data for users as well as process transactions on the network. They are rewarded in native AR tokens, which are minted by network node operators and serve as block rewards. Also like Bitcoin, Arweave was designed with a hard cap on the total supply (66 million AR tokens).
When users upload data, they pay AR tokens into the storage endowment, a reserve that keeps miners incentivized even if block rewards fall short. To sustain this mechanism of permanent storage in exchange for a one-time transaction, Arweave relies on two key assumptions:
- Storage gets cheaper over time (Kryder’s Law)
- AR token value remains steady or increases

Assumption 1 is backed by an observation from the storage industry called Kryder’s Law. According to Kryder’s law, storage density tends to double —and cost per unit tends to halve—roughly every 18 months. Historically, this has translated to an average annual storage cost decline of around 38%. Uploading data locks AR into the endowment, effectively removing it from circulation, which puts pressure on the price of AR tokens to increase.
So far, thanks to both assumptions holding, Arweave’s tokenomics has worked out, and as a result “not a single token has left the endowment since launch nearly 7 years ago.” However, if AR’s value fell significantly or storage costs stopped declining, the endowment could struggle to maintain incentives, jeopardizing Arweave’s long-term promise.
Swarm’s Redistribution Game
“Swarm is a peer-to-peer network of nodes that collectively provide a decentralised storage and communication service. This system is economically self-sustaining due to a built-in incentive system which is enforced through smart contracts on the Ethereum blockchain and powered by the BZZ token.” –Swarm whitepaper
In Swarm, the batch balance functions similarly to Arweave’s storage reserve, while the redistribution game can be likened to Arweave’s block rewards, keeping storage providers incentivized.
Users purchase postage stamps in bulk using BZZ (specifically, xBZZ on the Gnosis Chain). Individual stamps are attached to each data chunk uploaded to the DISC (Distributed Immutable Store of Chunks), Swarm’s underlying storage layer.
The BZZ tokens collected from postage stamp sales are redistributed to groups of nodes called neighborhoods. In each round of the game, a random neighborhood is selected to receive the reward, incentivizing cooperation and agreement on stored content.

The game is orchestrated by smart contracts. The batch also acts as a wallet, with storage rent deducted automatically based on the quota and the dynamic unit price set by the price oracle. The oracle adjusts the price of postage stamps based on supply and demand, specifically, how many nodes in the selected neighborhood are replicating chunks. If there are fewer than the target replication rate (of 4), the unit price increases; if more, it decreases. When exactly four attested replicas are present, the price remains stable.
As rent increases, stamps expire faster and associated data is deleted; when rent decreases, data persists longer. For this storage incentive model to work, Swarm relies on key assumptions:
- The number of nodes in a neighbourhood that participate in the game correctly indicates the supply of storage (for the size of reserve, a particular fixed volume of chunks each node is supposed to store).
- Liquid supply of storage: node operators will respond to price signals in the sense that higher prices will attract more node operators to dedicate their disk space to the network, while decreasing price will discourage some operators to continue their service.
If storage prices fall over time (as assumed in Arweave’s model) or if BZZ value increases, a well-funded batch can effectively achieve “pay once, store forever”. However, Swarm doesn’t make this a formal guarantee—rather, it allows flexible configurations based on user preferences and market conditions.
Comparing Risks and Assumptions
Let’s review the risks and assumptions side by side:
- Arweave depends on:
- Kryder’s law continuing to drive down storage costs
- A stable or rising AR token value
If both hold, the endowment can incentivize storage indefinitely.
- Swarm relies on:
- Accurate pricing via the price oracle and game participation
- Elastic node supply reacting to incentives
The unit price of rent (denominated in BZZ per chunk per block) is determined by a price oracle at the time the rent is due, so users can’t pre-determine how long storage will last.
But if the rent declines fast enough and the batch balance exceeds the finite sum of future rent, the balance will never deplete—effectively mimicking Arweave’s “store forever” outcome. Crucially, Swarm’s design allows users to set or adjust storage duration at any time. In this sense, Swarm’s economic model can subsume Arweave’s.
Conclusion
In essence, Arweave promises permanence via simplicity, locking in fixed assumptions at the protocol level. Swarm achieves resilience through adaptability, allowing price discovery and dynamic adjustments through market participation. For users, the choice boils down to:
- Arweave: Set-it-and-forget-it storage, assuming macroeconomic stability.
- Swarm: Adjustable permanence through market-driven economics.
Each has its strengths, and understanding their assumptions is key to deciding which is right for your data.
Unlocking True File Ownership: Swarm Desktop File Manager & Swarm Drive
In the ever-expanding universe of Web3, the dream of true digital sovereignty—where your data is undeniably yours, free from the clutches of centralized gatekeepers — is rapidly becoming a reality. At Solar Punk, we’re not just dreaming; we’re building the infrastructure that makes this future possible, facilitating applications of decentralized storage and communication on Swarm. Solar Punk is thrilled to give you a sneak peek into our latest innovations designed to empower you: the upcoming File Manager in Swarm Desktop and the powerful Swarm Drive proof-of-concept application!
Ushering in a New Era of Decentralized File Management: The Swarm Desktop File Manager
Imagine a world where managing your decentralized files is as intuitive as navigating your familiar cloud drive, but with all the inherent benefits of Web3: censorship resistance, privacy, and true ownership. That’s precisely what our upcoming File Manager for Swarm Desktop aims to deliver. This isn’t just a shiny new interface; it’s a fundamental shift in how you interact with your data on Swarm.
We’re meticulously crafting this File Manager with you, the user, at its heart. Our design principles are clear:
- Automation will handle complex Swarm operations in the background, like initial setup or basic postage stamp management.
- Assistance will guide you through essential steps, providing clear descriptions and sensible defaults for operations requiring user input.
- Clarity & Checkpoints ensure you always know what’s happening, especially for non-automatable actions, with explicit confirmations.
- Robust Error Handling will offer precise reasons and actionable recommendations if something goes awry.
- Asynchronous Operations will keep you informed on the status of large uploads or stamp creation/extension.
- User Value Focus means a familiar interface that abstracts away Swarm-specific details, unless needed or desired by advanced users.
A key innovation is the concept of a “Drive”—our user-friendly abstraction for a Swarm postage stamp, representing a distinct storage space where files are stored. You’ll be able to create and manage multiple “Drives,” each with its own capacity and lifetime (TTL) based on the underlying Swarm stamp. Need more space or longer storage? You can extend a Drive’s lifetime or increase its capacity with ease. We’ve even built in smart notifications to warn you when your “Drives” are running low on space or nearing expiration, suggesting proactive steps like extending capacity or lifetime.
The interface itself will feature a tree view for hierarchical navigation of your storage, alongside a browser view to display your content with columns like Name, Size, and Last Modified Date. You’ll be able to upload files via drag-and-drop or menu options, with progress indicators for asynchronous operations. The system supports managing version history, allowing you to view and restore previous versions of files. Restoring creates a new version, rather than deleting intermediate ones. You can rename files, which also creates a new version.
Regarding deletion, it’s important to understand that in most cases, deleting a file from the File Manager means its reference is removed from your view, but the underlying data remains on the Swarm network until its associated ‘Drive’ (postage stamp batch) expires or is explicitly destroyed. Due to the immutable nature of Swarm storage, selective file deletion is not yet available. However, this functionality may be introduced with future Swarm features, such as DREAM.
You can also open a “Get Info” panel for files and folders to view details such as size, Swarm hash, associated Drive, and expiration information. A detailed information window will provide an overview of all your Drives, metadata configuration, wallet information (BZZ and xDAI balance), and Swarm node status. You can also download files to your local machine when needed.
Swarm Drive PoC: Seamless Local-to-Decentralized Syncing
Complementing the intuitive File Manager, we’ve also been hard at work on the Swarm Drive proof-of-concept application. This is a lightweight command-line tool designed to seamlessly sync a local directory to Swarm, turning your decentralized storage into what feels like a personal, Swarm-backed “drive”.
Our goals for this PoC are ambitious yet focused:
- Zero-config: Minimal setup to get you started.
- Bi-directional awareness: It intelligently tracks changes both locally and on Swarm.
- Robustness: Ensuring safe uploads, deletions, manifest versioning, and the ability to resume from the last state.
- Extensibility: A clear architecture separating Swarm operations from other logic.
Swarm Drive allows you to perform familiar operations like backing up project folders. You can manually sync local changes to Swarm, watch a folder for auto-synchronization when files change, or even schedule syncing at specified intervals. This PoC demonstrates the behind-the-scenes mechanism that makes using Swarm as a regular storage medium a reality, focusing on the core challenge of keeping your local files in harmony with your decentralized storage. While it’s currently designed for Unix-based systems (initially Mac) and has some limitations as a proof of concept, it lays crucial groundwork for future integrations.
Building the Unstoppable Future, Together
Both the upcoming File Manager and the Swarm Drive PoC are testaments to Solar Punk’s unwavering commitment to making decentralized infrastructure accessible and powerful for everyone. We believe in a future where you, the user, have complete digital sovereignty. These tools, built on Swarm’s censorship-resistant and private architecture, are essential steps towards enabling self-sustained, decentralized, and unstoppable communities. Solar Punk helps facilitate building applications on the decentralized storage and communication infrastructure of Swarm.
Whether you’re a developer eager to integrate these cutting-edge capabilities into your Web3 applications or a business owner seeking robust, secure, and user-controlled decentralized storage solutions, Solar Punk has the expertise to guide you. We’re not just building tools; we’re cultivating an ecosystem where innovation thrives without the shadows of centralized control.

Beyond Folders and Tags: How Solar Punk’s OntoDAG can Lead to Smarter Data on Swarm
We navigate an ocean of data daily. While this abundance is powerful, effectively structuring it remains a fundamental challenge. Traditional methods like hierarchical folders or flat tagging systems often fall short, forcing us into rigid structures that don’t reflect the complex relationships between concepts. What if there was a better way, built for the decentralized web? At Solar Punk, we’re constantly exploring the frontiers of decentralized technology, pushing the boundaries of what’s possible on decentralized platforms, particularly Swarm. One of our exciting research initiatives, OntoDAG, tackles this very challenge of data organization head-on.
The Problem with Trees and Tables
Think about how you organize files today. You might use folders (a tree structure) or tags (like relational table attributes).
- Trees (Folders): Force a single hierarchy. Is a photo from Budapest in 2025 under Photos/Budapest/2025 or 2025/Photos/Budapest? Trees struggle with concepts that have multiple “parents” or belong to several categories simultaneously.
- Tables/Tags: Often require a fixed set of attributes for all items, which doesn’t work well when items have vastly different characteristics.
These limitations lead to clunky systems and often necessitate powerful search functions simply because the underlying organization is flawed.
As industry leaders have said before:
“If you have good categories, you don’t need to search. If you need to search, you lost something.”
Introducing OntoDAG: Order Theory Meets Decentralization
OntoDAG proposes a more flexible and intuitive approach based on Directed Acyclic Graphs (DAGs) and order theory. Think of a DAG as a graph where relationships flow in one general direction without forming loops, allowing for complex connections unlike simple trees. Instead of forcing data into restrictive trees or tables, OntoDAG allows for:
- Multiple Parents: Concepts can belong to multiple broader categories naturally.
- Rich Relationships: It models relationships more accurately than simple hierarchies.
- Structured Categories: Provides a semantic layer that’s more powerful than simple tags.
Essentially, OntoDAG aims to create a data structure that mirrors how we naturally understand and categorize information–as a network of interconnected concepts, rather than a rigid tree.
Why Build OntoDAG on Swarm?
Swarm’s decentralized storage and communication infrastructure provides the ideal foundation for a project like OntoDAG. Here’s why:
- Decentralized & Censorship-Resistant Storage: The OntoDAG structure itself, representing potentially vast knowledge graphs, can be stored securely and resiliently on Swarm, free from single points of failure or control.
- Foundation for Advanced Applications: OntoDAG isn’t just about storing the graph; it’s about using it. Swarm’s features enable powerful applications built on top of this structure.
Integration with Swarm Features: OntoDAG categories could potentially integrate directly with Swarm functionalities like the Access Control Trie (ACT), enabling sophisticated, category-based permissions.
Unlocking New Possibilities on Swarm with OntoDAG
OntoDAG is more than just a theoretical concept; it’s a research project exploring practical applications that showcase the versatility of Swarm. Imagine using OntoDAG on Swarm to power:
- Smarter Content Categorization: Replace cumbersome folder systems or tag clouds with a rich, ontology-driven structure for organizing files, media, or any data stored on Swarm.
- Dynamic Access Control: Define permissions using Swarm’s ACT based on an item’s position within the OntoDAG structure. For example, grant access to everyone in the “Project Alpha Team” category, which itself might be composed of sub-categories or individual roles.
- Contextual Communication: Create communication channels or social network groups defined by the ontology, ensuring relevant discussions and information flow.
- Decentralized Marketplaces: Use the ontology graph for sophisticated discoverability of goods and services, moving beyond simple keyword search.
- Membership Management: Gate content or features based on membership in organizations or groups defined within the OntoDAG.
These examples only scratch the surface. OntoDAG, as a research direction for Solar Punk, exemplifies how innovative data structures built on robust decentralized infrastructure like Swarm can unlock entirely new classes of applications–applications that are more intuitive, flexible, and user-empowering.
The Road Ahead
OntoDAG is an ongoing research project (see repo on GitHub). The roadmap includes refining the core concepts, developing implementations, creating APIs, and exploring deeper integration with Swarm–potentially augmenting Swarm’s native capabilities with specialized ways to handle OntoDAGs or function as a specialized graph database layer.
By exploring projects like OntoDAG, Solar Punk continues its mission to build the tools and infrastructure for a truly decentralized, resilient, and user-centric digital future, leveraging the power of foundational technologies like Swarm.
Stay tuned for more updates as we continue to explore the potential of OntoDAG and other innovations within the Swarm ecosystem!

Migrating from IPFS to Swarm: Your Guide to a More Resilient & Empowering Decentralized Web
Why Take the Leap to Swarm? Building a Better Foundation
IPFS and Swarm share the goal of decentralized storage, moving us away from centralized data silos. But if you’re looking to build truly resilient, self-sustaining, and user-empowering applications, Swarm offers compelling advantages.
While IPFS primarily provides a protocol for content addressing, Swarm is architected as a service. This crucial difference stems from Swarm’s built-in incentive layer, which economically motivates node operators to store and serve data, meaning content availability is fundamentally guaranteed within the network itself.
With IPFS, availability relies on active pinning, often requiring third-party pinning services and introducing points of dependency.
Swarm further distinguishes itself with superior privacy features and native encryption capabilities, notably through the Access Control Trie (ACT). Developed with contributions from the Solar Punk team, ACT offers fine-grained, on-chain access control, giving creators unprecedented flexibility and security over their data.
The table below shows the comparison of Swarm to IPFS.
| Feature | Swarm | IPFS |
| Data Availability | Guaranteed via incentivised storage and retrieval | No guarantees – relies on external pinning services |
| Retrievability | Native bandwidth market ensures persistent delivery | No native incentives for retrieval |
| Persistence Guarantees | Long-term through economic incentives | Ephemeral unless actively pinned |
| Privacy & Access Control | Built-in encryption and on-chain ACT permissions | No native encryption or access management |
| Censorship Resistance | High – fully decentralised with autonomous guarantees | Limited – centralised services can be pressure points |
| Architecture | Decentralised storage service | Decentralised protocol |
| Infrastructure Dependencies | Self-sustaining network | Typically needs third-party infrastructure |
| Target Use Case | Production-grade dApps with long-term requirements | File sharing and prototypes, not production storage |
Migrating to Swarm isn’t just changing storage; it’s a step towards reclaiming digital sovereignty, enhancing censorship resistance, and empowering users with greater control over their information.
How to Migrate: A Straightforward Path
The good news? Migrating your data from IPFS to Swarm is surprisingly straightforward. Because both systems utilize content-addressed storage, the core process involves retrieving your data from IPFS and uploading it to the Swarm network.
Prerequisites:
- Install Bee: If you haven’t already, get your Swarm node running. Follow the official guide: https://docs.ethswarm.org/docs/bee/installation/getting-started
- Install swarm-cli: You’ll need the command-line tool for interacting with your node: https://docs.ethswarm.org/docs/bee/installation/quick-start#install-swarm-cli
Fund Your Node: Ensure your Bee node has xDai and BZZ for transaction fees and postage stamps: https://docs.ethswarm.org/docs/bee/installation/fund-your-node/
Step 1: Get Your Swarm Postage Stamp
Uploading data to Swarm requires a “postage stamp,” which pays for storage over time. Purchase one using swarm-cli.
- Adjust –capacity (minimum 4GB, see the Effective Utilisation Table for guidance) and –ttl (time-to-live in days) as needed.
- Use a descriptive –label.
# Using newest swarm-cli (recommended)
swarm-cli stamp create –capacity 4GB –ttl 30d –label my-migration-stamp
# Note your Stamp ID (hash) from the output!
Note: If you have an older version of swarm-cli, use this instead of the above:
swarm-cli stamp buy –depth 17 –amount 600m –label my-migration-stamp –gas-price 10000000000
# (Adjust depth/amount based on capacity/TTL needs and check current gas prices)
Step 2: Identify Your Pinned Files in IPFS
List the root CIDs of the files and directories you want to migrate. Using -t recursive ensures you get only the top-level identifiers, not every underlying chunk.
ipfs pin ls –type=recursive
This command outputs a list of CIDs currently pinned on your IPFS node.
Step 3: Download from IPFS & Upload to Swarm (Single Item)
For migrating a single file or directory:
- Download from IPFS: Replace QmYourCID with an actual CID from Step 2.
ipfs get QmYourCID -o ./myFileOrFolder - Upload to Swarm: Replace MyStampID with the postage stamp ID you obtained in Step 1.
swarm-cli upload ./myFileOrFolder –stamp MyStampID
Swarm will return a Swarm Reference (hash) – this is your new decentralized pointer to access the content on Swarm!
Automating Migration for Multiple Files
For migrating multiple pinned items, this script automates the download-and-upload process. It downloads each pinned item from IPFS to a temporary directory, uploads it to Swarm, and cleans up successful migrations. Failed uploads remain in the temp folder for retrying.
#!/bin/bash
# Configuration
TEMP_DIR="/tmp/ipfs_migration"
STAMP="your-postage-stamp-hash" # IMPORTANT: Replace with your actual Swarm Postage Stamp hash
# Ensure required tools are installed
if ! command -v ipfs &> /dev/null || ! command -v swarm-cli &> /dev/null; then
echo "Error: ipfs and swarm-cli must be installed."
exit 1
fi
# Fetch all pinned CIDs (recursive type gets top-level items)
CIDS=$(ipfs pin ls --type=recursive | awk '{print $1}')
# Create temporary directory if it doesn't exist
mkdir -p "$TEMP_DIR"
# Process each CID
for CID in $CIDS; do
echo "Downloading CID: $CID..."
# Download from IPFS to the temporary directory
if ! ipfs get "$CID" -o "$TEMP_DIR/$CID"; then
echo "Error downloading CID: $CID. Skipping..."
continue # Skip to the next CID
fi
echo "Uploading to Swarm..."
# Upload the downloaded item to Swarm using the specified stamp
if ! swarm-cli upload "$TEMP_DIR/$CID" --stamp "$STAMP"; then
echo "Error uploading CID: $CID. Keeping file for debugging."
continue # Skip removal if upload fails
fi
# If upload succeeded, confirm and remove the temporary item
echo "Migration complete for CID: $CID"
rm -rf "$TEMP_DIR/$CID" # Remove the successfully migrated file/folder
done
echo "Batch migration complete!"Beyond Basic Migration: Building the Future on Swarm
As demonstrated, moving your data is technically simple thanks to the shared content-addressing foundation. But the implications are profound. By migrating to Swarm, you gain a truly persistent, economically sustainable, and privacy-preserving storage layer.
Imagine the possibilities this unlocks:
- Powering unstoppable decentralized applications (dApps)
- Securely hosting NFT metadata with guaranteed long-term availability
- Building censorship-resistant media streaming platforms
- Creating robust infrastructure for confidential data sharing
The move to Swarm is a move towards a more robust, autonomous, and user-centric internet.
Need Guidance? Let’s Build Together!
Whether you’re migrating a simple dataset, refactoring a complex application currently using IPFS, or exploring how to best structure your data to leverage Swarm’s unique features like ACT, Solar Punk is here to help! We have deep expertise in Swarm and are passionate about helping projects harness its full potential.
Get Started & Join the Movement:
- Experiment! Don’t hesitate to try the steps above with a small dataset.
- Explore: Dive deeper into Swarm’s documentation and concepts.
- Connect: Join the vibrant Solar Punk community on Galaxis to share your experiences and learn from others.
- Reach Out: Have questions or need tailored support for your migration? Contact Solar Punk – we’re excited to assist you in building the decentralized future.

Indexing NFT Metadata: Making Decentralized Assets Discoverable with Swarm
The world of Non-Fungible Tokens (NFTs) continues to expand, evolving beyond digital art into diverse applications like collectibles, gaming assets, and more. As the number of NFTs grows, the ability to efficiently index and search their associated metadata becomes increasingly crucial for both creators and collectors.
Imagine a vast library with countless books, but no catalog—finding what you’re looking for would be a daunting task. Similarly, without proper indexing, the rich information embedded within NFT metadata risks becoming lost in the decentralized web.
At Solar Punk, we believe in empowering developers and businesses with the tools to navigate and build on decentralized infrastructure. That’s why we’ve been deeply involved in exploring innovative solutions for managing NFT data on Swarm, the decentralized storage and communication network.
The Challenge of NFT Metadata Discovery
While the ownership of an NFT is recorded on the blockchain, the actual data describing the NFT—its name, attributes, associated media—is often stored off-chain. Traditionally, this metadata might reside on centralized servers, raising concerns about longevity, censorship, and single points of failure. Even when using decentralized storage solutions, effectively indexing and searching through large volumes of metadata presents a significant technical hurdle.
Swarm: A Foundation for Discoverable NFT Metadata
Swarm offers a robust and censorship-resistant platform for storing NFT metadata. Its decentralized peer-to-peer architecture ensures data availability and integrity, addressing the longevity concerns associated with centralized storage. Furthermore, Swarm’s content-addressed nature, where data is identified by a unique hash of its content, provides a strong foundation for verifiable and immutable metadata.
Solar Punk’s Insights
At the Swarm Summit 2024, Solar Punk presented key insights into indexing and searching NFT metadata with Swarm, going beyond traditional approaches. Our presentation outlined a vision for automatically cataloging image-based NFTs using AI tools.
The proposed process involves several steps:
- First, fetching the NFT image content and any existing metadata, if available.
- Then, an AI model is utilized to generate a short text description based on the NFT image. This descriptive text is subsequently processed using a Large Language Model (LLM) to extract a list of relevant keywords that highlight the NFT’s main features. For example, an image of a cat with a mohawk playing golf under a moonlit sky would be analyzed to generate keywords like “cat, mohawk, golf, moon”.
- Finally, an index is built from these keywords, enabling users to search for specific NFTs based on their visual attributes.
The resulting index structure would likely use a Suffix-trie and be scalable with shards, with the goal of ultimately uploading this index to Swarm to make it available anywhere. This approach aims to create a standardized way of indexing NFTs, improving the search experience in NFT marketplaces and enabling new applications for AI analytics in the NFT space.
Empowering the Future of NFTs
By focusing on solutions for indexing NFT metadata on Swarm, Solar Punk aims to:
- Enhance the utility of NFTs: Making metadata searchable unlocks new possibilities for discovering and interacting with NFTs based on their specific characteristics.
- Promote a more robust NFT ecosystem: Decentralized and easily discoverable metadata contributes to the long-term viability and value of NFTs.
- Simplify development for Web3 creators: Providing clear strategies—and potentially tools—for metadata indexing lowers the barrier to entry for building innovative NFT applications on Swarm.
As the NFT space continues its exciting trajectory, the need for effective metadata management will only grow. Solar Punk is committed to pushing the boundaries of what’s possible with decentralized technologies like Swarm, helping to build a future where digital assets are not only owned but also easily discoverable and accessible.
Stay tuned for more updates on our work in the NFT space and other exciting developments within the Swarm ecosystem. If you’re a developer or business owner looking to explore the potential of Swarm for your NFT projects, we’d love to connect. Let’s build a more discoverable and decentralized future together!

AI + Swarm – Decentralized Healthcare AI: Empowering Patient-Centric Medical Data
In our previous posts, we examined how decentralized AI can unlock secure and private financial modeling and reshape the very framework of intelligence. Today, we turn our focus to healthcare–a domain where data sensitivity and patient empowerment are paramount. Swarm’s robust, distributed infrastructure is well-suited to support Decentralized Healthcare AI, safeguarding sensitive medical data while driving advanced diagnostics and personalized treatment.
The Challenge of Centralized Healthcare Data
Traditional healthcare systems tend to consolidate sensitive patient information into centralized databases. This practice increases vulnerability to cyberattacks and unauthorized access, while limiting the control patients have over their own records. Without a decentralized framework, innovations in AI-driven diagnostics may be stifled by strict privacy concerns and risks associated with single points of failure. These challenges highlight the pressing need for a more secure, patient-focused approach to managing medical data.
How Swarm Can Enable Decentralized Healthcare
Swarm offers a transformative alternative by distributing data securely across a decentralized network. This approach mitigates the vulnerabilities of centralization while laying the groundwork for innovative AI solutions. By ensuring that each piece of information is encrypted, partitioned, and protected from potential breaches, Swarm not only secures sensitive medical records but also upholds the data sovereignty principles we examined in our previous post on decentralized AI for financial applications.
Privacy-Preserving Analytics in Healthcare
Swarm’s decentralized framework enables the development of privacy-focused analytical applications. This infrastructure allows developers to create solutions that securely process distributed data while preserving patient confidentiality. By employing federated learning alongside decentralized data aggregation, AI systems can extract meaningful insights from dispersed health data without ever transmitting raw, sensitive information. This approach ensures that patient privacy remains intact while still harnessing the power of advanced analytics, leveraging proven mechanisms now optimized for the unique challenges of healthcare.
Enhanced Data Sovereignty for Patients
Another cornerstone of Swarm’s solution is the Access Control Trie (ACT), which gives patients granular control over their medical data. Rather than relying on centralized oversight of institutions and large intermediaries that often dictate data flows, patients now decide who can access, modify, or use their health information. This shift away from reliance on traditional digital intermediaries–where data can be easily misappropriated–underscores a broader movement toward patient-controlled data, ensuring both heightened privacy and greater transparency in healthcare.
Improved Diagnostics and Treatment
With secure, decentralized data, AI-driven insights can pave the way for earlier disease detection and more tailored treatment plans. Picture an AI system that continuously scrutinizes distributed data to detect early signs of chronic conditions or customize interventions based on an individual’s unique health profile. Such advancements herald a new era in precision medicine, characterized by robust security, transparent data access policies, and truly personalized care.
Join the future of healthcare innovation with Swarm, where advanced AI diagnostics and patient-centric data control converge to create a secure, equitable, and transformative healthcare ecosystem.

The UK Wants to Ban Encryption – Again
The UK government is once again seeking expanded surveillance powers that would weaken encryption, reigniting a long-standing debate. This is not the first time lawmakers have sought to introduce legislation forcing tech companies to provide access to encrypted communications. Over the years, similar efforts have surfaced in different forms—from the controversial Investigatory Powers Act (IPA) of 2016 to more recent proposals targeting end-to-end encryption used by messaging apps and cloud services.
This debate is not limited to the UK. Other governments have made similar attempts, such as Australia’s Assistance and Access Act, the EU’s discussions around client-side scanning for CSAM detection, and the U.S. EARN IT Act. Each of these initiatives has faced resistance from privacy advocates and the tech industry, raising concerns about the unintended consequences of weakening encryption.
The Investigatory Powers Act and Its Evolution
Originally passed in 2016, the Investigatory Powers Act (often called the “Snooper’s Charter”) granted the UK government broad surveillance capabilities. Among its provisions, it required internet service providers to store browsing history for up to a year and gave intelligence agencies sweeping access to communications data. However, one of the most controversial aspects of the IPA has been its ongoing amendments, particularly those that aim to force companies to weaken encryption by providing government backdoors.
Apple and other tech firms have repeatedly resisted these efforts, arguing that any backdoor for government access could also be exploited by malicious actors. Despite industry pushback, the UK government periodically renews debates about encryption access, framing it as an obstacle to national security efforts rather than a fundamental privacy tool. If these legislative proposals advance, companies will face a tough choice: weaken security for all users or push back through legal and policy channels. Some tech firms have signaled they might reconsider their UK market presence if extreme regulatory measures threaten their encryption standards.
This isn’t just a UK issue–similar scenarios have played out globally. In response to laws requiring weaker encryption, Meta’s WhatsApp threatened to leave the UK, while Signal has made it clear it would rather shut down than compromise security. These cases highlight the broader industry response when governments attempt to undermine encryption.
Why “Only Spying on Bad People” Doesn’t Work
A common argument in favor of weakening encryption is that it will only be used to target criminals and terrorists. However, in practice, once encryption is compromised, it is compromised for everyone. Strong encryption protects not just activists, journalists, and dissidents but also businesses, governments, and ordinary citizens from cybercriminals, identity theft, and mass surveillance.
Encryption is not just a tool for privacy; it is a fundamental check within a democratic system. By ensuring that communication remains secure, encryption prevents any single entity—whether a government or corporation—from achieving absolute control over the flow of information. Legal frameworks rely on checks and balances to prevent overreach, and encryption serves as a technological safeguard that upholds these principles. Without strong encryption, centralized authorities could suppress opposition, stifle dissent, and undermine the mechanisms that allow for accountability and resistance in society.
Real-world examples demonstrate why this matters. Encrypted messaging has been vital for whistleblowers exposing corruption, journalists reporting on sensitive issues, and human rights defenders operating under oppressive regimes. Even businesses rely on encryption to protect trade secrets and prevent espionage. Weakening encryption wouldn’t just impact criminals—it would expose businesses, journalists, and everyday users to unprecedented risk.
Articles
- Washington Post – U.K. orders Apple to let it spy on users’ encrypted accounts
- BBC – UK demands access to Apple users’ encrypted data
- Tech Policy – UK Encryption Crackdown Imperils Privacy, Security & Free Speech
- Amnesty International – UK: Encryption order threatens global privacy rights
- Wikipedia – Encryption ban proposal in the United Kingdom

Join the Solar Punk Community on Galaxis and Build the Decentralized Future
Tired of centralized platforms controlling your data and limiting your online experience? In a digital world increasingly dominated by centralized platforms, the need for greater autonomy, security, and user control has never been more apparent. The Solar Punk community on Galaxis is your gateway to a more open, secure, and equitable Web3 world. We’re a community of passionate individuals dedicated to building and supporting decentralized applications on Swarm’s storage and communications infrastructure.
Our partner, Galaxis is a decentralized community platform that puts ownership and control back into the hands of creators and their communities. Through the use of NFTs and blockchain technology, Galaxis enables the creation of unstoppable communities free from the limitations and restrictions of traditional social media platforms.
The Solar Punk community on Galaxis is a vibrant hub for Web3 enthusiasts, developers, and anyone passionate about building a decentralized future. Here, members can connect with like-minded individuals, collaborate on projects, and stay informed about the latest advancements in the Swarm ecosystem.
Claim Your Free Community Membership Card
To become a part of this exciting community, simply follow these easy steps:
- Visit the Solar Punk Community Page: Go to https://galaxis-community.com/communities/solarpunk
- Connect Your Wallet: Ensure you have a Web3 wallet like MetaMask installed and connected to the Base mainnet with some ETH—a small amount will suffice to cover the minor transaction fee.
- Join the Community: Click the “Join the Community” button on the Solar Punk community page.
Mint Your Card: Click the “Mint” button and confirm the transaction in your wallet.
Benefits of Being a Part of the Community
As a Solar Punk community member, you’ll gain access to:
- Exclusive content and discussions: Stay informed about the latest developments in the Swarm ecosystem.
- Collaboration opportunities: Connect with fellow developers and build innovative projects together.
- Community events and activities: Participate in discussions, future workshops, and hackathons.
- A voice in shaping the future of Solar Punk: Contribute to the growth and development of a truly decentralized community.
Join the Movement
The Solar Punk community on Galaxis is more than a group of developers—it’s a movement toward a more equitable and decentralized digital future. By joining us, you’ll become a part of a passionate community that is shaping the future of Web3.
Claim your free Membership Card today and start building with us!

AI + Swarm – Unlocking the Power of Decentralized AI for Secure and Private Financial Modeling
In our previous post, we explored the risks of centralized AI and how Swarm offers a decentralized solution that prioritizes openness, security, and data sovereignty. Now, let’s delve deeper into a real-world use case and see how Swarm can revolutionize financial modeling while ensuring the privacy and security of sensitive financial data.
The use of AI in finance for tasks like risk assessment, fraud detection, and algorithmic trading is growing. However, the sensitive nature of financial data presents a challenge in maintaining its privacy and security. The answer lies in decentralized AI, and Swarm is at the forefront of this revolution.
The Challenge of Centralized AI in Finance
Traditional AI models rely on centralized platforms, which means your sensitive financial data is stored on third-party servers, potentially vulnerable to breaches, unauthorized access, and misuse. This centralized approach raises significant concerns about data privacy, security, and regulatory compliance.
Swarm’s Decentralized Solution for Financial AI
Swarm offers a groundbreaking alternative: a decentralized platform for building and deploying AI models that prioritize data security and privacy. Here’s how Swarm addresses the challenges of financial AI:
- Data Sovereignty: With Swarm, your data remains under your complete control. It’s encrypted and distributed across a decentralized network, ensuring no single entity has access to the entire dataset. This eliminates the risks associated with storing sensitive financial information on centralized servers.
- Privacy-Preserving AI: Swarm enables the development of privacy-preserving AI models, such as federated learning, where models can be trained on decentralized data without compromising confidentiality. This allows you to collaborate with others and leverage shared insights while maintaining the privacy of your own data.
Secure Access Control: Swarm’s Access Control Trie (ACT) allows you to define granular access permissions for your data and AI models. You can specify who can access, modify, or use your model data, ensuring only authorized individuals or entities can interact with your sensitive information.
Use Case: Secure Credit Risk Assessment
Imagine a decentralized credit scoring system built on Swarm. Individuals can retain ownership of their financial data, granting access only to authorized lenders. They can use Swarm’s access control (ACT) feature to ensure that they share their relevant data only with the financial provider of their choice. The provider’s purpose-trained and private AI models can then assess creditworthiness without exposing the underlying data, preserving privacy while enabling more accurate and equitable credit risk assessments.
This approach can be extended to various other financial services. For instance, investment firms can use Swarm to analyze market trends and individual portfolios privately, offering personalized advice without compromising client data. Insurance companies can assess risk profiles and tailor policies based on secure, decentralized health records.
The Future of AI is Decentralized
Swarm is paving the way for a new era of agentic AI that prioritizes security, privacy, and individual control. By providing a decentralized storage and communication infrastructure for all kinds of AI use cases, Swarm empowers individuals and organizations to harness the power of AI while safeguarding their sensitive financial data.
Join the decentralized finance revolution with Swarm and unlock the full potential of AI in finance and beyond!

AI + Swarm – A New Paradigm for Decentralized Intelligence
Introduction
AI is advancing at an unprecedented pace, but who controls its future? The concentration of power in a few well-funded organizations raises concerns about transparency, ethics, and access.
Nearly half of OpenAI’s long-term risk researchers have left the company in recent months, according to former governance researcher Daniel Kokotajlo. Meanwhile, OpenAI’s leadership has admitted that even $1 billion is not enough to compete with AI giants like Google and Facebook. The AI arms race is accelerating, and with it, the risk that AI development will be dictated by a select few.
What happens when one of the most powerful technologies in human history is controlled by centralized entities? Is there an alternative—one that prioritizes openness, security, and decentralization?
The Risks of Centralized AI
Today, AI models are predominantly hosted on centralized platforms like OpenAI, Google, and Microsoft. While these platforms offer powerful services, they also control access to AI models and data, determining who gets access, under what conditions, and whether access can be revoked based on financial, political, or regulatory pressures.
This concentration of control creates significant risks. When AI is centralized, corporations and governments have the power to dictate its direction. They can restrict access to certain technologies, suppress innovation, or even limit access to models and data based on their own interests. This means AI could become a tool of influence, controlled by those with the most resources, rather than serving the broader needs of society. It’s a scenario where access to transformative technology could be withheld or manipulated based on economic interests, geopolitical considerations, or corporate agendas.
Without a decentralized approach, AI could become a technology reserved for only the privileged, limiting accessibility and preventing wider, more equitable access. This is not just a question of fairness, but also one of opportunity. If AI remains in the hands of a few powerful entities, it risks being shaped by their priorities rather than being an open resource that benefits all humanity. The question remains: who controls AI, and at what cost to innovation, transparency, and freedom?
What Swarm Offers
Swarm provides a censorship-resistant, decentralized data layer that enables open access to AI models and datasets for everyone. With the introduction of ACT (Access Control Trie), users can enforce access control without intermediaries. This empowers individuals and organizations to manage their own data securely, free from reliance on corporate gatekeepers.
With access control, users can determine who can access their data, ensuring privacy and autonomy. At the same time,choosing to make AI models open enables provable provenance, allowing for transparent tracking of the origin and ownership of AI models and datasets. This balance between control and transparency ensures both privacy and accountability.
References
“Nearly half the OpenAI staff that once focused on the long-term risks of superpowerful AI have left the company in the past several months, according to Daniel Kokotajlo, a former OpenAI governance researcher.”
https://fortune.com/2024/08/26/openai-agi-safety-researchers-exodus
“On Monday, OpenAI’s leaders said that a paltry $1 billion wouldn’t be enough to compete with the well-resourced AI labs at companies such as Google and Facebook after all.”
https://www.wired.com/story/compete-google-openai-seeks-investorsand-profits

Galaxis Partners with Solar Punk and Swarm to Revolutionize the Future of Decentralized Communities
In an era defined by rapid digital transformation, decentralization has shifted from being a mere option to a necessity. Amid growing concerns over data ownership, privacy, and censorship, platforms championing Web3 principles are paving the way toward a more secure and user-centric future. In this context, Galaxis—a platform committed to empowering creators and fostering communities—has announced its collaboration with Swarm decentralized storage and communication infrastructure, and Solar Punk. Together, they aim to unlock the full potential of decentralized storage solutions.
A Collaborative Step Toward Decentralized Ecosystems
This partnership represents an important step toward creating environments where online communities can thrive without relying on centralized systems. By combining Galaxis’s innovative tools with Swarm’s robust infrastructure and Solar Punk’s technical expertise, they are laying the groundwork for dynamic and unstoppable decentralized ecosystems that offer greater autonomy and security.
The Power of Decentralized Storage
At the heart of this partnership is Swarm’s peer-to-peer (P2P) storage architecture. Unlike traditional centralized solutions, which are vulnerable to failures or interference, Swarm distributes data across a global network of nodes. This ensures that data remains accessible, secure, and censorship-resistant.
For communities using the Galaxis platform, this approach offers several significant benefits:
- No single entity can control or remove data.
- Advanced encryption protects user interactions and metadata from prying eyes.
- Swarm can scale alongside growing communities and decentralized applications, adapting to their evolving needs.
By integrating Swarm’s capabilities, Galaxis is building a foundation for private, stable, and self-sovereign community spaces.
Solar Punk’s Role in the Vision
Solar Punk’s experience in building decentralized solutions complements Galaxis’s vision for sustainable, decentralized communities. This partnership is focused on more than just storage—it aims to create tools that enhance how communities interact online. Planned features include:
- Supporting open discussions without fear of external interference.
- Enabling private, real-time connections among community members.
- Leveraging blockchain to dynamically manage permissions based on on-chain activities.
Enhancing the Galaxis Experience
For users of the Galaxis platform, this partnership introduces tools and features designed to empower both creators and communities:
- Each community will have its own Swarm node, ensuring autonomy and resilience.
- Multi-chain support for Swarm postage stamps makes decentralized storage user-friendly.
- Moving community assets, such as images to metadata, from IPFS to Swarm will provide greater stability and privacy.
These enhancements align with Galaxis’s mission to equip creators with the freedom to innovate, offer members secure engagement, and enable communities to thrive free from external constraints.
Looking Ahead
The collaboration between Galaxis, Solar Punk, and Swarm embodies the broader values of Web3—decentralization, user empowerment, and resilience. As concerns over data security and censorship grow, Galaxis is focused on developing practical solutions that prioritize privacy, autonomy, and innovation.
This partnership underscores a shared commitment to building tools that make online communities more secure and independent. By integrating cutting-edge storage solutions with innovative community-building features, they are creating online spaces that are safer, more autonomous, and firmly rooted in Web3 principles.

How NFTs Can Last Forever: Solving the Security Challenge
NFTs (Non-Fungible Tokens) continue to evolve beyond digital art and collectibles. In this series of posts, we’ll explore some of the most important trends shaping the NFT space in 2025.
Are NFTs as Secure as They Seem? Let’s Discuss.
To kick things off, let’s tackle one of the biggest hurdles facing NFTs today: long-term security and accessibility. Have you ever wondered what happens to your NFT if the server hosting the artwork goes offline? Many NFTs are linked to external files stored on centralized servers, raising critical questions about their longevity.
If the server fails or the provider removes the file, your NFT may still prove ownership of… a broken link. Similarly, while an NFT proves ownership of the token itself, it doesn’t necessarily guarantee copyright protection for the associated artwork. Unauthorized distribution and copyright enforcement remain significant challenges, further highlighting the gap between owning an NFT and controlling the asset it represents.
How can we ensure that the artwork remains secure and accessible over time? Share your insights below, and stay tuned as we dive deeper into this topic and explore possible solutions in the next post.
Here’s How NFTs Can Truly Last Forever
In our previous post, we discussed the risk of losing the artwork tied to your NFT if the server hosting it goes offline. This concern resonates with many NFT owners and creators, as centralized storage systems often leave digital assets vulnerable to server failures or removal by hosting providers.
The good news is that decentralized storage solutions, like Swarm, offer a reliable remedy to these challenges. Swarm provides an immutable and provable storage infrastructure for NFT content, ensuring that the artwork remains accessible and secure over time. By integrating Swarm’s content-addressed hash into an NFT’s on-chain record, creators can guarantee both availability and authenticity.
Here’s how Swarm addresses these challenges:
- Permanent Storage: Swarm’s decentralized nature eliminates reliance on centralized servers. Even if individual nodes become unavailable or temporarily offline, the artwork remains accessible.
- Content Integrity and Provenance: The content-addressed hash acts as a unique fingerprint for the artwork, ensuring its integrity and immutability. Any modification to the file results in a different hash, providing a verifiable link between the NFT and its content. This also makes it easier to prove provenance and assert copyright claims.
- Provable Availability: Swarm enables verifiable claims about data availability, allowing anyone to confirm that the artwork associated with an NFT is securely stored and accessible.
By leveraging Swarm’s technology, NFT creators can enhance the longevity and security of their digital assets, addressing the risks posed by centralized storage solutions. This not only strengthens the connection between NFTs and their underlying content but also builds a more resilient ecosystem for digital ownership.

Decentralized Multimedia Libraries Released
The decentralized web is evolving rapidly, bringing with it the need for scalable, censorship-resistant multimedia solutions. To support developers building these next-generation experiences, we are thrilled to announce the release of the first version of our Multimedia Middleware libraries.
These libraries are specifically designed to facilitate the development of decentralized multimedia and social networking applications on the Swarm infrastructure. They address the growing demand for censorship-resistant platforms by providing cost-effective and scalable building blocks for developers. Our broader aim is to drive mass adoption of the Swarm protocol by making it easier for developers to create on-demand and streaming multimedia applications as well as social media platforms.
Developed as part of Solar Punk’s Fellowship with the Swarm Foundation, these libraries deliver unstoppable, censorship-resistant multimedia solutions, including group chat and audio/video streaming. Released as NPM packages and written in vanilla JavaScript, they ensure broad compatibility across a variety of JavaScript frameworks.
Libraries Released
The initial release includes the following libraries:
Audio-Video Live Streaming Library
This library enables media streaming and playback over Swarm and manages live audio/video streams by utilizing Swarm Feeds. It is compatible with any browser that supports the WebM format.
- NPM package: @solarpunkltd/swarm-stream-js.
- Code repository github.com/Solar-Punk-Ltd/swarm-stream-js and an
- Example implementation: github.com/Solar-Punk-Ltd/swarm-stream-react-example.
Live Group Chat Library
The live group chat library facilitates real-time messaging over Swarm using the GSOC (Graffiti Several Owner Chunks) feature. It leverages multiple nodes for improved performance.
- Main GSOC nodes handle incoming messages
- Writer nodes write messages to Swarm Feeds
- Reader nodes load messages.
Other notable features include tracking present users via keep-alive messages and a mechanism to prevent spam.
- NPM package: @solarpunkltd/swarm-chat-js
- Code repository: github.com/Solar-Punk-Ltd/swarm-chat-js
- Example project: github.com/Solar-Punk-Ltd/swarm-stream-react-example
Comment System Library
This library supports dynamic comment walls on Swarm by using Swarm Feeds to write comments at appropriate indexes for individual or range-based access.
- NPM package @solarpunkltd/comment-system
- Core codebase: github.com/Solar-Punk-Ltd/comment-system
- UI code repository github.com/Solar-Punk-Ltd/comment-system-ui, including a web widget for HTML embedding and a React component for seamless integration with React applications.
How Developers Can Build on Swarm
These libraries can be used to create a wide range of decentralized multimedia applications, such as:
- Social Media Platforms: Build censorship-resistant platforms where users can post text, audio, and video content using the chat and streaming libraries, while enabling them to comment with the Comment System.
- Streaming Services: Create live streaming and on-demand video platforms that are resistant to censorship, allowing creators to distribute content without platform restrictions and monetize it directly.
- Metaverse Environments: Utilize the libraries as building blocks to create immersive metaverse experiences that require real-time communication, media streaming, and comment functionality.
By using these libraries, developers can significantly reduce development costs and time-to-market for customized social media and multimedia platforms. These tools facilitate the creation of diverse applications, contributing to the growth of the Swarm ecosystem. As the demand for storage increases in the Swarm network, it will further strengthen the network’s overall value and drive sustainable growth.
Ready to Build the Future?
Future enhancements to these libraries will include additional chat and comment features, such as message threads and likes. The streaming library will also undergo continuous evolution to ensure ease of use and provide top-notch performance for decentralized media applications.
Our measure of success lies in the adoption of these libraries by developers looking to build performant, unstoppable, and censorship-resistant applications. Explore these libraries, join our developer community, and let’s work together to bring your unique Web3 experiences to life!

A Year in Review: Solar Punk’s 2024 Milestones for Developers and Business Owners
As we wrap up 2024, the Solar Punk team reflects on a remarkable year of growth, innovation, and engagement with the decentralized technology community. From leading presentations at global events to making strides in decentralized storage, this year has been pivotal in shaping the Web3 ecosystem.
Let’s review the year behind us! It began with a visit to NFT.NYC where we explored the latest developments in NFT and related technologies. Spring took us to ETH Prague, immersing ourselves in the evolution of the Ethereum space. In June, we were key participants at the Swarm Summit, presenting our advancements and plans for enabling developers and businesses to harness Swarm’s capabilities. We closed the year at Devcon in Bangkok, where we showcased a Swarm-based application and hosted a side event to connect with fellow developers and businesses interested in integrating our technologies.
This post revisits Solar Punk’s 2024 milestones and highlights the opportunities they create for developers and business owners.
Swarm Summit 2024
In June, after the collaborative Hack Days, Solar Punk presented at the Swarm Summit, sharing key insights on how developers can leverage Swarm for efficient, secure, and scalable applications. Our team delivered five impactful presentations on essential topics for integrating decentralized solutions:
- Indexing and Searching NFT Metadata with Swarm
- Access Control Over Swarm Content
- Swarm Light Node as a Mobile Application
- Running a Swarm Node Inside a Browser
- Decentralized Media Streaming over Swarm
The response from the audience was overwhelmingly positive, with many developers and businesses expressing interest in applying Swarm’s technologies to improve their own solutions. Our discussions underscored Swarm’s flexibility and scalability while highlighting its transformative potential across industries, including NFTs and media streaming.
Introducing Access Control: Enhancing Data Security and Flexibility
A key Solar Punk contribution to Swarm is the Access Control Trie (ACT), an advanced encryption and key management system largely based on the architecture outlined in Viktor Trón’s Book of Swarm. ACT offers precise control over content access, making it invaluable for developers and businesses requiring secure decentralized storage.
By using public-key cryptography and secure key derivation, ACT enables content publishers to grant or revoke access as needed, unlocking a wide range of use cases, including:
- Content Monetization: Secure subscription-based content delivery.
- Private Data Sharing: Safeguarded exchange of sensitive business or personal data.
- Decentralized Platforms: Controlled-access private social networks.
ACT was officially integrated into the Swarm protocol with the release of Bee Node version 2.2.0 in September, paving the way for its adoption in decentralized applications and services.
Devcon.buzz: Showcasing Social Media Functions on Web3
At Devcon7 in Bangkok, Solar Punk unveiled Devcon.buzz, a decentralized app built entirely on the Swarm network. The app provided attendees a privacy-focused platform to connect, share ideas, and explore Web3 technologies.
Devcon.buzz also demonstrated how businesses can create bespoke decentralized applications prioritizing data security and user control. Applications using this framework might include:
- Social networks where user data is secure and privacy is paramount.
- Metaverse-like experiences where interactions are decentralized, transparent, and secure.
This project exemplifies Solar Punk’s ability to help businesses transition to decentralized systems, unlocking new possibilities in user engagement and collaboration.
Swarm Fellowship: Empowering Developers with New Tools
In October, Solar Punk was honored to receive a Swarm Foundation Fellowship for developing libraries that simplify decentralized application development. These libraries streamline the process by offering:
- Pre-built components and tools for common Web3 functionalities like social media platforms and advanced metaverse experiences.
- Increased accessibility, simplifying integration with Swarm’s infrastructure.
- Enhanced standardization and interoperability within the Swarm ecosystem.
For businesses, this means faster deployment of decentralized solutions, lower development costs, and a more robust infrastructure for their applications. Whether you’re looking to build a decentralized social network or an enterprise-grade solution, these libraries significantly simplify the process, helping to bring your ideas to life more quickly and efficiently.
Partnership with Galaxis: Empowering Community Creators
Solar Punk partnered with Galaxis.xyz to bolster the security and resilience of their platform for online community creators. This collaboration birthed the Solar Punk Community, a hub for developers to explore our technologies and collaborate.
With all assets stored on Swarm, the roadmap envisions communities running entirely on Swarm’s decentralized peer-to-peer network. This ensures censorship resistance and data breach protection, allowing businesses to build unstoppable operations.
Looking Ahead
2024 has been an exhilarating year of progress for Solar Punk. As we continue to innovate, our commitment to empowering developers and business owners with decentralized technologies remains steadfast. Whether building a Web3 application, integrating decentralized storage, or creating secure platforms, Solar Punk has the expertise to guide your journey.
Stay tuned for updates as we expand possibilities for decentralized applications in the Web3 ecosystem. If you’re a developer or business owner ready to explore these technologies, we’d love to connect with you.
Let’s continue building the future together in 2025!

Devcon SEA Recap: A Milestone for Solar Punk and a Night to Remember at Rooftop Buzz
Devcon has always been more than just an event for the Web3 community—it’s a celebration, a reunion, and a space to forge new paths for the future of blockchain. This year’s Devcon SEA was especially significant for our team, as it marked our first, but certainly not the last, participation. The energy, connections, and ideas we encountered made for an unforgettable experience.
What Solar Punk Gained from Devcon SEA
For Solar Punk, Devcon SEA was the perfect stage to release our anonymous communication platform, Devcon.buzz, showcase our latest projects, connect with key players in the ecosystem, and strengthen our ties within the community. We established numerous meaningful connections with developers, enthusiasts, and industry leaders who share our commitment to a decentralized, sustainable future.
Throughout the event, we engaged in conversations that have already sparked new ideas and collaborations. Meeting like-minded individuals and teams underscored just how much potential lies in collective innovation. Each connection brought fresh insights, potential partnerships, and shared goals that will shape our future work.
Rooftop Buzz Side Event: A Night of Networking
A highlight for Solar Punk was our Rooftop Buzz side event at ANJU Korean Rooftop Bar on November 14th. We hosted an incredible evening for developers, blockchain enthusiasts, and community members, creating a relaxed yet vibrant atmosphere where ideas flowed freely and connections were made in the beautiful sunset over Bangkok.
The turnout exceeded our expectations, and the rooftop venue provided the perfect setting for meaningful conversations and inspiration against the backdrop of the city lights. It was a privilege to see so many people come together—from seasoned blockchain veterans to newcomers excited about what the future holds.
A Look Ahead: Building on Devcon’s Momentum
Leaving Devcon, the Solar Punk team is more motivated than ever. The event was not only a significant milestone for us but also a powerful reminder of the collaborative spirit within the Web3 community. The discussions and connections made at Devcon and Rooftop Buzz have created momentum that will propel us forward as we continue to work toward a sustainable, decentralized future.

Solar Punk Rocks Devcon SEA with Devcon.buzz — And You Can Benefit From It!
The future is bright, and it’s powered by the sun… and Swarm. Solar Punk, a pioneering force in the decentralized web, is making waves at Devcon with groundbreaking tech that pushes the boundaries of Web3 social media.
If you’ve been following Solar Punk, you know we’ve already captivated the Web3 community by showcasing multimedia streaming on Swarm. But hold onto your hats, because at Devcon, we’re unveiling something even bigger: decentralized commenting and chat.Forget centralized servers and data harvesting. Solar Punk is introducing devcon.buzz, an open, anonymous, and privacy-focused app built specifically for Devcon7 attendees. This app lets participants experience firsthand the power of truly decentralized communication on Swarm.
What’s in it for you as a developer or business owner?
Integrate just two essential Swarm components into your project:
- Access Control Tries (ACT): Developed by Solar Punk, ACTs give users granular control over who can access their data on Swarm.
- Swarm Feeds: Swarm’s unique feed structure enables efficient and secure content updates.When combined with ACTs, this creates the ideal foundation for subscription models and paywalled content.
The implications are huge.
Imagine a world where social networks are owned by users, not corporations. A world where censorship is impossible and privacy is the default. That’s the world you can help create with Solar Punk and these groundbreaking technologies.
Want to shape the future with us?
Solar Punk is ready to invest time and resources to help bring your decentralized vision to life. We’ll work closely with you to:
- Clarify your business model: Explore revenue streams, tokenomics, and sustainable growth strategies.
- Define technical components: Identify the best tools and technologies for your project.
- Outline development needs: Create a roadmap for building and deploying your decentralized application.
Ready to take the next step?
- Join us at Rooftop Buzz, our Devcon side event on November 14th: Connect with the Solar Punk team and discuss your project in person. Register here!
- Reach out to us: Exchange your contact information with our CSO, Daniel Weber, and we’ll get back to you.
Let’s build a brighter, decentralized future together!

Solar Punk Libraries: Empowering developers and businesses in the Web3 era
Solar Punk is thrilled to announce that it has been honored with a prestigious Fellowship from the Swarm Foundation. This accolade recognizes Solar Punk’s commitment to revolutionizing multimedia delivery and social networking. With this Fellowship, Solar Punk will accelerate the development of its audio, video streaming, and chat libraries on Swarm’s decentralized infrastructure. As a result, developers and business owners will be able to tap easier into the vast potential of the Swarm network, creating unstoppable, censorship-resistant applications that will drive innovation, increase user adoption, and support the growth of the entire Web3 community.
As the Web3 landscape rapidly evolves, the demand for decentralized social media platforms and censorship-resistant communication tools is growing exponentially. The Solar Punk project aims to meet this need by developing audio, video streaming, and chat libraries powered by Ethereum Swarm’s decentralized infrastructure. These libraries offer developers and business owners a unique opportunity to tap into the potential of the Swarm network and create innovative multimedia applications.
Benefits of Solar Punk libraries for Developers
- Decentralised and Censorship-Resistant: The Solar Punk libraries enable developers to build applications that are resistant to censorship and manipulation, ensuring that content remains accessible and unalterable.
- Versatile Streaming Capabilities: Supporting both on-demand and live audio/video streams, the libraries give developers the flexibility to create a wide range of multimedia applications.
- Easy Integration: Written in Vanilla JS, the libraries are compatible with various JS frameworks, making integration seamless and efficient.
Benefits of Solar Punk libraries for Business Owners
- Cost-Effective and Time-Saving: By leveraging the Solar Punk libraries, businesses can significantly reduce development costs and accelerate time-to-market for customised social media platforms and metaverse-like experiences.
- Scalability and Reliability: The Swarm network’s decentralised infrastructure ensures scalability and reliability, allowing businesses to handle large volumes of multimedia content without compromising performance.
- Monetisation Opportunities: The project anticipates potential revenue streams through direct project delivery and the sale of additional libraries with advanced features, providing businesses with sustainable monetisation strategies.
The Solar Punk libraries are poised to revolutionise how developers and business owners approach multimedia delivery and social networking in the Web3 era. They provide the essential building blocks for creating unstoppable, censorship-resistant applications that will drive innovation, increase user adoption, and support the growth of the Swarm ecosystem.

Devcon.buzz: a decentralized communication app for Devcon
Introduction
Devcon.buzz is a groundbreaking decentralized web application built on Swarm, designed to transform communication at Devcon. This innovative app offers a secure and private platform for real-time chatting, leveraging Swarm’s capabilities to decentralize all components. By providing a comprehensive conference agenda, organizing discussions by agenda points, and enabling anonymous chat, Devcon.buzz enhances the Devcon experience and fosters a vibrant community.
Technical overview
Swarm is a decentralized storage and communication infrastructure that operates as a peer-to-peer network, designed to facilitate a self-sovereign digital society. It provides a scalable, base-layer infrastructure for the decentralized internet, ensuring permissionless publication and user privacy. The decentralized nature of Swarm ensures data is resistant to censorship.
Swarm’s Bee nodes are accessed through a network of gateways that act as entry points into the decentralized storage environment. Users send HTTP requests to a Swarm gateway, which retrieves the requested data from the Swarm network, abstracting the complexities of directly interacting with a peer-to-peer protocol and allowing users to leverage Swarm’s functionalities using standard web protocols.
To make Devcon.buzz accessible to everyone, even those without any experience with Web3 or Swarm, we use familiar cloud services as an entry point to the actual decentralized mechanisms running under the hood. We went with Google Cloud’s Cloud Run service to set up a few services easily, and provide on-demand scaling for these out of the box.
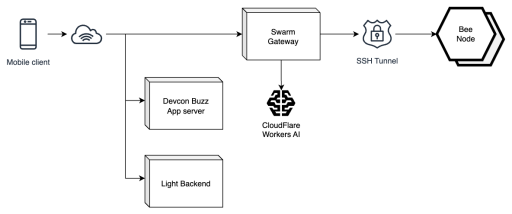
We deploy three limited-scope services on Cloud Run, each with a distinct function:
- Devcon Buzz App server: Serves the Reactive client-side code and acts as the app’s entry point behind the devcon.buzz web domain.
- Light Backend: Handles essential features requiring server-side processing, like assigning unique nicknames and managing the app’s gamified elements.
- Swarm Gateway: Bridges the traditional cloud and the decentralized Swarm network.
A fourth service, an SSH Tunnel runs as a VM in Google Cloud Compute. This is a crucial component to provide a secure connection between the Swarm Gateway instances in Google Cloud and Bee nodes within the Swarm network. It wraps outgoing requests and sends them over an encrypted SSH connection to machines hosting Bee nodes.
To promote safety and respect compliance requirements of Devcon and its host country, Thailand, we have introduced an opt-in content filtering mechanism. To avoid human moderators accessing and reviewing uploaded content, we utilize AI and one of the newest open-weight LLMs, the LLama 3.2 3B. For an effective and robust solution we do this via calling the API of CloudFlare’s Workers AI.
This is the extent of components needed to run on traditional cloud service providers, limited to the minimum to be able to achieve the smoothest experience possible and simplifying onboarding for the application’s users.
All content generated through the app—comments on Devcon talks, Buzz Space chat messages, and private notes—is stored on Swarm, guaranteeing Devcon.buzz’s private, highly available, and censorship-resistant nature. And by the way, the complete agenda of Devcon as displayed in the application is loaded directly from Swarm too!
Using your own local Bee Node
If you want the truly fully decentralized experience, you will be able to run Devcon.buzz with your own Swarm Bee node either on a desktop or with a Bee node running on your mobile device. This removes the need for gateways, allowing users to upload and download their app content directly from Swarm.
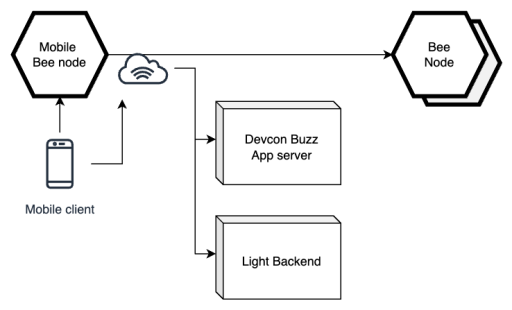
With some future work it might become possible to host the Reactive app directly from Swarm. Until then, the Devcon.buzz App server or a local package will host the app’s code. Calling the Light Backend will still be needed until a decentralized compute solution could be introduced.
User Experience
Let’s have a look at the cool features of the Devcon.buzz app, what makes them work behind the scenes, and how they are built on top of Swarm’s decentralized infrastructure.
Agenda and Comments
The Devcon agenda is uploaded to Swarm and remains updatable, so any changes to the schedule can be synced even during the event. Swarm’s Feed structure makes this dynamic updating possible.
Each agenda talk has its own comment wall for users to share their thoughts. This is implemented using Swarm’s Graffiti feed mechanism, which allows multiple participants to contribute to the same feed, driven by the Comment System library.
Live Chat (Buzz Spaces)
To keep the discussion vibrant and alive, each Devcon category (Core Protocol, Layer 2s, etc.) has its own Buzz Space. For these Spaces we wanted to showcase a novel solution capable of managing live group chat in a fully decentralized manner. Two of its key components are a list of active chat participants which is maintained throughout the lifecycle of the chat, and individual user feeds for message sending.
Maintaining the list of active participants is done by one or multiple Bee nodes acting as aggregators which track the last activity per user and register new joiners to the chat on a dedicated feed. In the chat code library, there will be an option to perform the aggregation on the client-side. This can be managed by an active user selected through a round-robin mechanism, further decentralizing the process.
We will release the code libraries for the live chat and the Comment System soon, complete with documentation, so anyone can create censorship-resistant communication channels on Swarm.
Private Notes on Swarm
Devcon.buzz also enables users to write private notes, which are stored on Swarm via the Feed structure. Each note will have its unique topic, organizing them neatly under a single feed. Updates to notes keep previous versions accessible, with the latest always at the most recent index.
Conclusion
Devcon.buzz offers a powerful set of features for Devcon attendees, streamlining the conference experience with a comprehensive agenda, organized discussions, and anonymous chatting to build community. Its true strength lies in its decentralized foundation on Swarm, ensuring security and resilience.
Looking ahead, Devcon.buzz has the potential to be much more than a conference app. Its decentralized architecture makes it a valuable tool for any community seeking secure and private communication. This project exemplifies Swarm’s vast utilities and its potential to revolutionize online communication, paving the way for a future of decentralized applications that empower users while protecting their privacy and data integrity. As the technology continues to mature, Devcon.buzz and similar projects are positioned to lead the transition to a truly decentralized web.
Devcon.buzz: Revolutionizing Communication with Anonymous Chatting on Swarm
Devcon7, a landmark gathering for developers from across the globe, is set to witness a seismic shift in how attendees connect and communicate. Amidst growing concerns about data privacy and centralized control, Solar Punk, a visionary tech collective, has stepped up to answer the call with a groundbreaking new app, Devcon.buzz.
Devcon7 and it’s audience
Devcon is a biannual conference that brings together Ethereum developers and enthusiasts to explore the latest advancements and future potential of blockchain technology. This community is acutely aware of the risks posed by centralized platforms that collect, store, and often exploit user data— a reality underscored by recent issues with once-trusted social platforms. The audience longs for a communication platform where they can freely exchange ideas and collaborate without sacrificing their privacy.
Devcon.buzz: the power of anonymous chatting
Anonymous chatting offers a solution to this pressing need. It empowers users to engage in open and honest discussions without fear of having their personal information tracked or misused. This feature resonates deeply with the Devcon7 vision of fostering a secure, unstoppable, and censorship-free space for brainstorming, problem-solving, and knowledge-sharing.
Solar Punk’s solution
Solar Punk’s app, built on the decentralized architecture of Swarm, revolutionizes communication at Devcon7. It leverages Swarm’s robust capabilities to provide a secure and private platform for real-time chatting, with all components fully decentralized.
The app streamlines the Devcon experience by:
- Providing a comprehensive conference agenda: Attendees can stay organized and up-to-date with sessions and events.
- Organizing discussions by agenda topics: This helps users to easily connect with like-minded individuals and engage in relevant conversations.
- Facilitating anonymous chatting: Users can freely express ideas without compromising their privacy.
- Rewarding active participation: Encouraging users to explore Swarm’s features and contribute to the network’s growth.
The impact
This app demonstrates the potential of Swarm to revolutionize real-time communication in a truly decentralized manner. By empowering Devcon7 attendees to connect and collaborate anonymously, Solar Punk has not only addressed a major concern of the Devcon7 audience but also set a new standard for data privacy in the digital age.
The combination of the app’s features and the decentralized nature of Swarm creates a unique and powerful communication tool for Devcon7 attendees. It fosters a sense of community and encourages open dialogue while ensuring that users retain control of their privacy.
Join the conversation at Devcon7 and experience the future of communication on Swarm with Devcon.buzz!

Bee 2.2.0 is Here: Empowering Developers and Node Operators
The much-anticipated Bee 2.2.0 upgrade has successfully gone live!
This update brings game-changing features and enhancements that will transform how developers and node operators interact with Swarm. Let’s break down what these changes mean, even if you’re not a tech expert.
What’s the Big Deal About Bee 2.2.0?
In a nutshell, Bee 2.2.0 makes Swarm more powerful and user-friendly.
- For Developers: Imagine you’re a content creator. Now you can decide exactly who gets to see your work—down to individual pieces. Want to offer exclusive content to subscribers? No problem. This level of control is possible thanks to a new feature called Access Control Trie (ACT). For developers, we have an extensive post explaining the underlying tech here and also discuss the new opportunities it opens for business models here.
- For Business owners: With the introduction of the Access Control Trie (ACT) in Bee 2.2.0, business owners now have unprecedented control over who can access their content on Swarm. This feature unlocks exciting new opportunities for new business models. For instance, content creators can offer exclusive content to their subscribers or provide tiered access based on different membership levels. ACT enables businesses to monetize their content more effectively and build stronger relationships with their audiences. You can read more about it here.
- For Node Operators: Node operators are the backbone of Swarm, ensuring its smooth operation. This upgrade allows them to relocate to less congested network regions, increasing their chances of earning rewards from the reward pool. Additionally, node operators gain greater flexibility in managing their stake (a type of deposit needed to participate in the network).
The Tech Behind the Upgrades
- Access Control Trie (ACT): This system acts as a highly secure lock for your content. Unlike other solutions, ACT empowers you to create and manage discrete access keys for specific wallet addresses.
- Neighborhood Hopping: Picture the Swarm network as a bustling city. If one neighborhood gets too crowded, node operators can now move to a quieter one. After syncing with their new neighbors, they help to create a more robust network in general and get rewarded to do so.
- Partially Withdrawable Stake: This gives node operators more control over their stake, letting them withdraw some of it while still keeping the network secure.
- Optimized Peer Connections: Think of this as streamlining the network. Nodes now connect to an optimal number of peers, with stronger and more stable connections, making the entire infrastructure run smoother.
Important Reminder
If you’re a Swarm user, make sure you’re using Bee version 2.2.0 or newer. This ensures you get all the benefits of this major upgrade.
The Future of Swarm
Bee 2.2.0 is a major step forward for Swarm. It empowers developers to create new and exciting applications while improving the experience for node operators. The Swarm network is becoming stronger and more capable, and we can’t wait to see what the future holds.

Ethereum Swarm’s Erasure Coding: error correction on a higher level
While data replication is a basic method of data protection, it can be expensive and lacks inherent error detection, making error correction codes like erasure coding crucial. Hamming codes, an early error correction method, detect errors using parity bits, but struggle with multiple errors. Modern error correction techniques break data into pieces with added redundant information, enabling both detection and correction of errors efficiently.
Erasure coding is an advanced error correction method that ensures data can be recovered even when parts of it are lost or corrupted. It’s particularly valuable in distributed storage networks like Swarm, where data is spread across multiple nodes, making it vulnerable to failures or outages.
Swarm’s decentralized structure naturally splits data into chunks, making erasure coding an ideal protection method. It ensures that even if multiple nodes (or neighborhoods) go offline, the original data can still be recovered, improving reliability and opening Swarm to enterprise use cases.
Erasure coding provides a cost-effective, robust solution for safeguarding data, making it essential for decentralized networks aiming to offer high data availability and security.
How Erasure Coding works
Erasure coding works by splitting data into N chunks and adding K additional chunks for redundancy. These N + K chunks are distributed across the network, and as long as at least N chunks remain retrievable, the original data can be fully reconstructed. This allows systems to tolerate the loss of up to K chunks, making erasure coding far more resilient than traditional error correction methods like Hamming codes, which can only detect and correct bit-level errors within a chunk (one chunk is 4KB in size).
For example, if you split an 8KB file into two chunks (N=2) and add one redundant chunk (K=1), you can lose one chunk and still recover the file. By increasing K, you can tolerate the loss of more chunks, providing greater protection.
Benefits of Erasure Coding
- Efficiency: Erasure coding provides better protection than replication while potentially using less bandwidth, meaning faster download speeds. For instance, an N=2, K=2 erasure code requires 16KB to store an 8KB file, offering the same fault tolerance as simple replication, but the file can be retrieved by downloading any 2 chunks.
- Complete Data Loss Protection: Unlike Hamming codes, which only fix small errors, erasure coding can recover entire lost chunks of data, making it ideal for large distributed systems.
Why Erasure Coding is a game changer for businesses
For businesses, erasure coding offers a highly reliable and cost-efficient solution for data protection, especially in environments requiring long-term storage or high availability. Enterprises dealing with critical data, such as financial institutions, healthcare providers, or cloud service companies, can benefit from erasure coding’s ability to reduce storage overhead compared to traditional replication. Its resilience against data loss, even in the face of hardware failures or network outages, makes it ideal for industries that need robust disaster recovery and continuity strategies. By leveraging erasure coding, businesses can achieve greater data durability, reduce costs, and ensure compliance with stringent data protection regulations.
Unlocking New Business Models: Introducing Access Control (ACT) in Swarm’s Decentralized Storage Network
Swarm, a groundbreaking decentralized data and distribution network with its unique features not only makes your assets censorship resistant and unstoppable, but also revolutionizes data access management with its brand new feature called Access Control Trie (ACT).
Here we explain what ACT is, explore its diverse business applications, and highlight the advantages of partnering with Solar Punk at an early stage of the project planning.
So what are Access Control Tries (ACTs)?
As one explores the complexities of decentralized storage systems, it becomes apparent that uploaded assets are essentially made public within the network. While encryption alone is a protective measure to prevent unauthorized access without the decryption key,at the same time it undermines your sovereign control over who can access the data. The potential for key compromise or covert retrieval poses a significant challenge. For business models that depend on the intrinsic value of data assets and aim to monetize them, a more robust and flexible solution is vital.
ACT is an innovative decentralized access control solution designed specifically for Swarm. It empowers users to grant and revoke access to specific assets, associate access with unique Web3 wallet addresses, and dynamically manage access permissions. For an in-depth understanding of the technology, we encourage you to explore this article Introducing the Access Control Trie (ACT) in Swarm.
Business Applications areas that could immediately benefit from ACT on Swarm
The ability to control access of individual assets complements Swarm’s unique content management capabilities very well. Let us quickly list a few areas as examples where the addition of Access Control opens the gate for entirely new business models.
Content creation and distribution
Swarm is ideally suited for publishing any kind of content particularly audio and video thanks to its native support for efficient P2P streaming. In addition by incorporating Swarm feeds, versioned access to content can be offered. The integration of ACT into the protocol now allows easy and dynamic gating and monetization of stored content or specific versions of it. Furthermore, by integrating payment solutions into the model, ACT can be utilized to create subscription-based services, including streaming platforms.
Communications
Swarm is more than a storage network; it also functions as a robust communication platform. Feeds within Swarm empower users to establish group chats or even complete social networks. The Access Control feature of Swarm plays a pivotal role in this regard, enabling the creation and dynamic management of private groups and even entire gated communities that feature secure interactions.
Data management and cooperation
Businesses can securely store and share confidential data, collaborate seamlessly on sensitive projects yet maintain data integrity.
Apart from usual internal file sharing and collaboration a typical example could be the storage of supply chain metadata. For example certain parts of the dataset, such as origin and transfer locations should be visible to everyone, while other data, such as transfer prices and conditions should only be available to specific selected users or groups.
Solar Punk is your ideal collaborative partner
Solar Punk being the team behind the implementation of ACT into the Swarm protocol stands out as a trusted partner for all businesses seeking to integrate Swarm technologies into their existing applications and systems.
Whether you already have a desired architecture in mind or you are just at the business concept phase we recommend talking to us. We are not just a team of experienced developers and engineers who offer custom development services, but we can also help you to figure out how Swarm can add value to your business model.
Do you have a concept in mind? Would you work with us on the next project? Contact us!
Key takeaway
ACT combined with Swarm’s unique features, presents a transformative opportunity. Businesses across various industries can unlock new opportunities by partnering with Solar Punk in integrating the technology into their infrastructure. Our expertise and unwavering dedication to customer success guarantee a smooth and effective implementation empowering businesses to leverage the full potential of decentralized technologies and drive innovation in their respective domains.

Optimized chunk production for compact usage of postage buckets: A Swarm Hack Week success
During the recent Swarm Hack Week, the Solar Punk team hosted a hackathon where Mirko from Etherna developed a project aimed at addressing the inefficiencies in postage batch consumption in Swarm’s data storage. Currently, storing data in Swarm requires purchasing postage batches with a depth much larger than necessary, leading to significant inefficiencies and increased costs. The project focused on optimizing this process to make the nominal space in postage batches truly usable.
Steps of development
Using Bee.Net, an open-source C# library, he introduced a “compaction level” ranging from 0 to 100. This compaction level controls the effort put into compacting chunks within buckets. At level 0, there is no effect on chunk compaction, while at level 100, the compaction is maximized. The compaction level sets a trigger limit on bucket collisions, prompting the system to mine a better chunk hash when collisions occur. To enhance precision at higher compaction levels, he implemented this using a parabolic function.
Mirko added a custom byte in front of each data chunk’s payload to enable the mining of different chunk hashes, resulting in data chunks containing 4095 bytes of actual information instead of the original 4096 bytes. To interpret these optimized chunks, the reader simply drops the first byte of each data chunk. This approach ensures that the optimization can be executed solely on the client side, though it would be more efficient if handled server-side.
The key advantages of this approach include making nominal space in postage batches usable, reducing postage batch costs, and not requiring additional resources for storing decryption keys. The algorithm works even if not all chunks within the postage batch are optimized, and different files can utilize different compaction settings, enhancing flexibility.
If you would like to take a closer look on the project’s code, you can reach it on the following link: https://github.com/Etherna/bee-net/tree/feature/BNET-99-swarm-hackathon-2024
Future work
Future work will focus on developing a deterministic method for hash production to enhance consistency, refining the trigger level formula for better performance at lower levels, and investigating solutions for the potential impact of unoptimized chunks on lower depths due to the birthday paradox.
This Swarm Hack Week project has significantly advanced the optimization of Swarm’s storage. By implementing a compaction level and optimizing data chunks, he has made Swarm’s storage more efficient and cost-effective. This collaborative innovation exemplifies the potential for future improvements in decentralized data storage. Stay tuned for more updates as we continue to enhance Swarm’s capabilities!

Fake IDs & Fraudulent KYC: Can Crypto Find Salvation in Swarm-Powered Decentralisation?
The “OnlyFake” scandal, exposing the ease of bypassing KYC checks with forged IDs, throws a spotlight on the vulnerabilities of centralised verification systems in crypto. But fear not, for decentralisation and Swarm, a leading decentralised data storage and distribution technology, might hold the key to a more secure and empowering future.
Centralised KYC: A Honeycomb for Hackers and Fraudsters
Storing user data on centralised servers creates a honeypot for malicious actors. Deepfakes become potent weapons, exploiting weak verification processes to jeopardise financial security and erode trust. Opaque verifications further exacerbate the issue, leaving users with little control over their data and fostering privacy concerns.
Swarm & Decentralization: Empowering Users, Fortifying Security
Decentralisation offers a paradigm shift. By storing user data on blockchains like Swarm, a distributed and tamper-proof ledger, we eliminate central points of attack. Users regain control through self-sovereign identities, fostering trust and transparency. But how do we verify attributes without exposing sensitive information?
Zero-Knowledge Proofs: Verifying Without Revealing
Zero-knowledge proofs (ZKPs) act as cryptographic shields. They allow individuals to prove they possess certain characteristics (e.g., being above 18) without revealing any underlying data. This guarantees privacy while maintaining the integrity of verification.
A Glimpse into the Future: Secure & Empowering Crypto Identity Management with Swarm
Imagine a world where:
- Swarm-powered decentralised storage eliminates honeypots, making data breaches a distant memory.
- ZKPs render deep fakes useless by focusing on attribute verification, not identities.
- Users hold the reins of their data, fostering trust and transparency within the ecosystem.
Here’s how Swarm and ZKPs could work together:
- Store ID data on Swarm: Users upload their encrypted ID documents to the decentralised Swarm network, ensuring data privacy and distribution across multiple nodes.
- Zero-knowledge verification: When required, users leverage ZKPs to prove they possess necessary attributes (e.g., age) without revealing the entire document.
- Empowered control: Users maintain complete control over their data, deciding who can access specific attributes and revoking access as needed.
The “OnlyFake” incident serves as a stark reminder of the need for change. By embracing Swarm-powered decentralisation and ZKPs, we can create a crypto space where security, privacy, and user empowerment reign supreme.
The question now lies with you: Are you ready to join the movement towards a more secure and empowering crypto future?

Understanding Erasure Coding in Distributed Systems: A Guide to Swarm’s Innovative Approach
Introduction to Data Storage in Distributed Systems
In our increasingly digital world, the importance of effective and secure data storage cannot be overstated. Distributed systems, such as cloud storage networks, represent a significant advancement in this area. These systems distribute data across multiple locations, ensuring accessibility and resilience against failures or data losses. However, this distributed nature also introduces unique challenges in terms of data storage and retrieval. For instance, ensuring data integrity and availability across different nodes in a network becomes more complex. Understanding these challenges is crucial for appreciating the innovative solutions like Swarm’s erasure coding, which are designed to address these specific issues.
Overview of Erasure Coding in Swarm
Imagine you have a jigsaw puzzle, and even if a few pieces are missing, you’re still able to recognise the picture. This analogy aptly describes the principle behind erasure coding, a method used for protecting data in distributed systems like Swarm. In Swarm’s context, erasure coding is not just a safety net for missing data; it’s a strategic approach to ensure data is both secure and optimally stored. This coding technique involves dividing data into chunks, then adding additional ‘parity’ chunks. These extra chunks allow the system to reconstruct the original data even if some chunks are lost or corrupted, much like how you can still make out a picture with a few missing puzzle pieces.
Comparison with Traditional Methods
Traditional data storage methods often rely on redundancy—storing multiple copies of data across different locations. While this approach is straightforward, it’s not the most efficient, especially in terms of storage space and resources. In contrast, erasure coding, as used in systems like Swarm, presents a more sophisticated solution. It strikes an optimal balance between data availability and storage efficiency. By storing additional parity information rather than complete data copies, erasure coding provides a reliable means of data recovery with less overall storage requirement. This efficiency makes it particularly suitable for distributed systems, where resource optimization is key.
Deep Dive into Swarm’s Erasure Coding
Swarm’s implementation of erasure coding through Reed-Solomon coding is a masterclass in data protection. This method, at its core, involves breaking down data into manageable chunks, followed by the creation of additional parity chunks. These extra chunks act as a safety mechanism, allowing for the reconstruction of the original data, should any part be lost or corrupted. It’s a method that mirrors the intricacies of a well-crafted puzzle, where each piece, even if minor, plays a crucial role in the bigger picture. This intricate process not only ensures data integrity but also bolsters the system’s ability to recover from unforeseen data losses.
Real-World Applications in Swarm
In practical scenarios, Swarm’s use of erasure coding is a game-changer, especially in maintaining data integrity and availability. In real-world applications, such as cloud storage services, this translates to an unparalleled reliability for users. Whether it’s safeguarding critical business documents or preserving cherished family photos, Swarm’s system ensures that users’ data remains intact and retrievable, even in the face of partial data losses. This level of reliability and security is what makes Swarm stand out in the crowded field of data storage solutions.
Benefits Specific to Swarm’s Approach
Swarm’s unique approach to erasure coding brings with it a suite of advantages. The enhanced data security that comes from this method is the most prominent, providing a robust shield against data loss. Moreover, the system’s efficiency in data storage is noteworthy; by reducing the need for redundant data copies, it significantly cuts down on storage requirements. This efficiency is not just about saving space – it’s also about optimising resources and reducing costs, making it a highly cost-effective solution for large-scale data storage needs.
Technical Challenges and Solutions
The implementation of erasure coding in Swarm, while beneficial, is not without its complexities. Managing the intricate balance between data accessibility, integrity, and storage efficiency presents a significant challenge. However, Swarm’s sophisticated coding techniques and network management strategies have been meticulously designed to address these issues. By continually refining these strategies, Swarm ensures a seamless and reliable user experience, maintaining its status as a leader in distributed data storage.
Conclusion
Erasure coding in distributed systems like Swarm marks a significant milestone in digital data storage and protection. In an era where data’s value is ever-growing, the importance of technologies like erasure coding cannot be understated – they are essential for the reliability and security of our digital world.

Zero-Knowledge Rollups and Ethereum Scalability: The Future of Interoperability
In recent weeks, the world of blockchain technology has witnessed a surge in the launch of projects centered around zero-knowledge proofs. Notable offerings include Polygon’s zkEVM, Matter Lab’s zkSync Era on the Ethereum mainnet, and ConsenSys’ Linea zkEVM on the testnet. These projects share a common goal: to enhance Ethereum’s scalability by harnessing the power of zero-knowledge proofs. In this article, we delve into this exciting development and explore the potential future of interoperability in the realm of zero-knowledge rollups.
Zero-Knowledge Proofs: The Foundation
Zero-knowledge proofs are cryptographic techniques that allow one party to prove they possess specific knowledge without revealing the actual knowledge itself. In the context of blockchain technology, these proofs enable Ethereum to scale efficiently. Rollups, a key concept in this context, offload the computation for thousands of transactions from the main Ethereum blockchain, providing a tiny cryptographic proof that validates the correct execution of these transactions.
Competing Rollups or Collaborative Harmony?
As these zero-knowledge rollup projects gain momentum, a pressing question arises: Is it a winner-takes-all competition among them, or can they coexist harmoniously, working together seamlessly? Anthony Rose, head of engineering for zkSync, envisions a future where multiple rollups can collaborate, making it irrelevant for users to choose a specific one. In his view, the rollups will become an integral part of the blockchain infrastructure, much like how users of platforms like Snapchat or Facebook don’t need to understand the technical intricacies of the internet.
Interoperability: The Bridge to the Future
Transitioning from a landscape of competing rollups to an ecosystem of interoperable and composable zero-knowledge solutions is a significant challenge. Fortunately, the community is already contemplating this transition, and all the zero-knowledge projects mentioned are working on plans to achieve interoperability to varying degrees. The extent of this interoperability, however, largely depends on the development of standards and protocols.
Ethereum Scalability: Current Status
Currently, Ethereum’s scalability faces practical limitations due to data availability on the network. Despite various solutions claiming theoretical scalability figures in the tens of thousands of transactions per second (TPS), the reality is different. Ethereum and its scaling solutions collectively process around 25 transactions per second, with Ethereum itself averaging about 12 TPS over the past month. Arbitrum One, Optimism, and zkSync offer TPS in the range of 1.6 to 7.2.
The Road to Interoperability
Interoperability between rollups is crucial to prevent users from being confined to isolated ecosystems. For instance, Optimistic Rollup users experience a one-week waiting period for fund withdrawals, limiting their ability to interact with other ecosystems. Achieving interoperability is technically possible, but its practical implementation depends on factors such as the financial viability of frequently putting proofs on Ethereum, which currently results in delays of 10 to 20 minutes between transactions.
Interoperability vs. Composability
It’s important to distinguish between “interoperability” and “composability.” While these terms are often used interchangeably, they have distinct meanings. Interoperability involves the seamless movement of funds between different layer-2 solutions. Composability takes it a step further, enabling transactions that involve operations across multiple rollups. Achieving composability may require the development of new standards and protocols.
The Role of MetaMask Snaps
MetaMask, a popular browser wallet, offers another avenue for achieving interoperability. They are developing Snaps, which are crowdsourced wallet extensions that extend MetaMask’s capabilities. Snaps could facilitate communication between different ZK-rollups, allowing them to interact with each other effectively.
Composability: The Future Frontier
Composability entails transactions involving operations on different rollups in a more real-time manner. This requires the development of new standards and protocols, and the sooner this happens, the better the user experience will be. With synchronous composability, transactions can be seamlessly executed across different off-chain systems, offering users an optimal liquidity experience.
The Potential of Optimism’s Superchain
Optimism introduces the concept of a “Superchain” that aims to integrate various layer-2 solutions into a single interoperable and composable system. Shared sequencing and the separation of proving and execution are key aspects of this concept, allowing cross-chain operations like flash loans to occur efficiently.
Direct Connection between ZK-Rollups
Some experts believe that ZK-rollups can connect directly with each other, as long as they can verify each other’s proofs. Smart contracts can be written to interpret incompatible proofs used by different rollups, enabling direct communication. This approach simplifies interoperability, especially when rollups share a common codebase.
Towards an Interoperable and Composable Future
In summary, the future of Ethereum scalability is expected to revolve around interoperability and composability among various zero-knowledge rollup solutions. These advancements will be driven by the development of standards, protocols, and collaborative efforts among the blockchain community. As these systems mature, users and developers alike will benefit from a more interconnected and efficient Ethereum ecosystem.

Understanding Decentralised Data Storage Costs on Ethereum Swarm
In the dynamic world of blockchain technology, Ethereum Swarm stands out as a cornerstone for decentralized data storage and communication. It’s crucial for users and developers in the Ethereum ecosystem to understand the intricacies of storage costs on this platform. This article delves deeper into the various factors affecting these costs, including network size, data size, and the critical role of BZZ tokens in pricing.
What is Ethereum Swarm
Ethereum Swarm is not just a decentralized storage system; it’s an extension of Ethereum‘s vision to build a comprehensive, decentralized internet. It enables data to be stored and distributed across a network of nodes, reducing reliance on centralized servers and mitigating risks like data loss or censorship. Swarm is designed to seamlessly store Ethereum’s dApp data, smart contracts, and user data, ensuring high availability and resistance to outages.
Factors Influencing Storage Costs
Network Size: The cost of data storage on Swarm is significantly influenced by the network’s size. A larger network means more nodes are available to store data, leading to increased redundancy and potentially lower costs due to economies of scale. In contrast, a smaller network might have higher costs due to increased demand for the limited storage space available.
Data Size: The volume of data being stored directly impacts the cost. Larger files require more space and network resources, naturally incurring higher costs. Smaller data sets, however, are less resource-intensive, making them more economical to store.
The Role of BZZ Tokens
BZZ tokens, Swarm’s native cryptocurrency, are fundamental to its operational model. These tokens facilitate transactions within the Swarm network, serving as a form of payment for storage services. Users pay for storage in BZZ, while node operators earn BZZ by providing storage space. This creates a decentralized market for storage, where prices are governed by supply and demand.
The Pricing Mechanism
Swarm’s pricing model is dynamic, adjusting to real-time conditions in the network. Storage costs are calculated based on several factors, including the amount of data, network congestion, and the availability of nodes. This ensures that the pricing is fair, competitive, and reflective of the network’s current state.
Swarm’s Postage Stamps Mechanism
An integral part of understanding data storage in Swarm is its unique “postage stamp” system. This mechanism is crucial for the functioning of the Swarm network and influences storage costs:
- Concept of Postage Stamps: In Swarm, users must purchase “postage stamps” to upload and store data. These stamps are essentially proof of payment attached to the data being stored, ensuring that the data remains in the network for a predetermined amount of time.
- Functioning: When a user wants to store data, they buy a postage stamp using BZZ tokens. The price of the stamp depends on the size of the data and the desired storage duration. The data with a valid postage stamp is then accepted and stored by the nodes in the network.
- Impact on Storage Costs: The cost of postage stamps adds an additional layer to the overall storage costs on Swarm. It’s a pay-as-you-go model where the more data you store and the longer you want it stored, the more postage stamps you need to purchase.
Understanding Swarm’s Cost Per Gigabyte Per Year
Calculating the cost of storing data, such as a gigabyte for a year on Ethereum Swarm, requires an understanding of several dynamic factors:
- Market Value of BZZ: Since storage costs are paid in BZZ tokens, the market value of BZZ significantly impacts the cost. As the value fluctuates, so does the cost of storage.
- Network Demand and Supply: Costs vary depending on the balance between available storage space and the demand for storage. Higher demand or limited supply can drive up costs.
- Data Redundancy and Replication: Swarm ensures data redundancy for reliability, which might affect the cost as more copies of the data are stored across different nodes.
Given these variables, providing an exact figure for the cost per gigabyte per year can be challenging. However, for illustrative purposes, let’s assume a scenario:
Assume that 1 BZZ equals X USD, – you can check the up to date prices here – and the current rate for storing 1 GB of data for a month is Y BZZ – check the up to date Swarm storage price here. Therefore, the cost to store 1 GB of data for a year would be (Y * 12) * X USD. At the time of writing, based on this calculation you’d pay $1.561 for storing one GB of data for a year on Swarm. It’s important to regularly check the latest rates and BZZ value for the most accurate cost estimation.
Comparisons with Other Storage Solutions
When compared to other decentralized storage systems like IPFS (InterPlanetary File System) and Filecoin, Swarm offers a distinct approach. While IPFS focuses on peer-to-peer file sharing and content addressing, Swarm provides more integrated storage solutions specifically designed for the Ethereum ecosystem. Filecoin, with its unique proof-of-storage model, represents another alternative, highlighting the diversity in decentralized storage solutions.
Future Outlook and Scalability
The future of Swarm is closely tied to the broader development of the Ethereum ecosystem. As Ethereum evolves, so too will Swarm, potentially leading to more efficient storage solutions and cost reductions. Key to this evolution will be improvements in scalability and network efficiency, which are expected to impact storage costs positively.
Conclusion
Grasping the nuances of storage costs on Ethereum Swarm is vital for anyone engaged in the Ethereum ecosystem. The cost is influenced by factors like network size, data volume, and the economic model governing BZZ tokens. As Swarm continues to grow and evolve, staying informed about these developments is crucial for developers and users alike.

Worldcoin’s Integration with Major Platforms: A Leap Towards Mass Adoption and Decentralised Data
In an unprecedented move marking a milestone towards mass adoption of decentralised technologies, Worldcoin has unveiled its latest version of the World ID feature, dubbed “World ID 2.0”. This groundbreaking update, as announced on Dec. 12, has integrated with major platforms including Shopify, Mercado Libre, Reddit, Telegram, and notably, Minecraft, significantly broadening its reach and utility.
Embracing Decentralised Identity Verification
World ID 2.0 is more than just an authentication tool; it’s a harbinger of a new era in digital identity verification. By enabling users on platforms like Shopify and Mercado Libre to prove their humanness without compromising personal data, Worldcoin is setting a new standard in user privacy and data security. This aligns perfectly with our ethos, where we are committed to building custom-made dApps on top of Ethereum Swarm – a testament to the power and potential of decentralised data layers.
The Impact of Zero-Knowledge Proofs
Central to Worldcoin’s approach is the implementation of zero-knowledge proofs – a technology that allows one party to prove to another that a statement is true, without revealing any information beyond the validity of the statement itself. This is crucial for maintaining privacy and security in decentralised systems. In the context of World ID 2.0, it means that users can verify their identity without exposing their biometric data, addressing one of the most significant concerns in the digital world today.
Reducing Fraud and Enhancing User Experience with World ID 2.0
The integration of World ID 2.0 with these platforms is a significant step towards reducing the losses that retailers face from return fraud, bots, and coupon stacking – estimated at a staggering $100 billion a year. For instance, Shopify stores can now create coupons and specify the level of humanness required for redemption, ranging from device-verified to Orb-verified levels. This not only enhances security but also improves the overall user experience by streamlining authentication processes.
Paving the Way for the Future
As a company at the forefront of decentralised application development, Solar Punk recognizes the monumental significance of such integrations. They represent a shift towards a future where decentralised data is as pivotal as Bitcoin and Ethereum have been. The adoption of World ID 2.0 by major platforms like Minecraft, which has a vast and diverse user base, is a testament to the scalability and versatility of these technologies.
Conclusion
The integration of World ID 2.0 with major platforms marks a significant stride towards the future of decentralised data and digital identity verification. We envision a world where blockchain technology is seamlessly integrated into everyday life, enhancing security, privacy, and user experience. We are witnessing a pivotal moment in the journey towards a decentralised, secure, and user-centric digital world.

Mastering Digital Sovereignty: Unlocking the Power of Decentralised Data
A Paradigm Shift in the Digital World
In the rapidly evolving landscape of blockchain technology, a new narrative is unfolding – one where decentralised data stands as a cornerstone, akin to the groundbreaking emergence of Bitcoin and Ethereum. Today, our digital existence, encapsulated in browser history and sensitive information, is often exploited. This exploitation, largely unseen, leads to significant and sometimes alarming consequences.
Reclaiming Control: The Essence of Digital Sovereignty
The rise of digital interactions has paradoxically led to a loss of control over our digital identities. This trend highlights the urgent need for heightened awareness and protection of our online data. High-profile data breaches, like MGM’s and recent cybersecurity incidents involving major crypto platforms, have laid bare the vulnerabilities inherent in centralised systems.
Decentralisation vs. Digital Sovereignty: Understanding the Difference
While these terms are often used interchangeably, they encapsulate different aspects of online autonomy. Digital sovereignty is about controlling and owning your online identity, leveraging tools that ensure self-governance of personal data. Decentralisation, on the other hand, is the architectural distribution of control, aimed at reducing dependency on single entities and creating a more resilient digital ecosystem.
The Role of Decentralised Data in Empowering Users
Decentralised data is not just about the technical redistribution of control; it’s about crafting a digital landscape where users can assert their sovereignty. By adopting decentralised structures, like those found in blockchain technology, users gain more autonomy over their digital interactions, ensuring that their data remains secure, private, and within their control.
Embrace the Digital Sovereignty Movement
As we step into this new era, the call to embrace digital sovereignty grows louder. It’s no longer sufficient to be passive participants in the digital realm. Instead, we must actively engage with technologies that empower us, ensuring that our digital trails are not exploited but protected. Decentralised data offers a path to this future, one where each individual’s digital identity is safeguarded and respected.
The Journey Toward a Sovereign Digital Identity: Embracing Ethereum Swarm with Solar Punk’s Expertise
As we journey toward a future underpinned by digital sovereignty, the role of decentralised data becomes increasingly crucial. Ethereum Swarm emerges as a pivotal technology in this landscape, offering a robust platform for creating fully decentralised applications. This technology not only ensures data security and privacy but also aligns with the ethos of a decentralised, user-empowered digital world.
For those looking to harness the full potential of decentralised data in their dApp development, Solar Punk is here to guide and assist. Our expertise in building on Ethereum Swarm enables us to help you create dApps that are not just technologically advanced but also deeply committed to the principles of digital sovereignty and user autonomy.
We encourage you to explore the possibilities that Ethereum Swarm offers. If you’re ready to embark on this path and want your project to stand at the forefront of digital innovation, reach out to us here. Together, we can build a future where digital ownership and creativity are fully harnessed through the power of decentralised data.

A Beginner’s Guide to NFT dApp Creation and Launching: Best Practices
In the ever-evolving landscape of blockchain technology, two phenomena stand out for their transformative potential: Non-fungible Tokens (NFTs) and Decentralised Applications (dApps). While they serve distinct purposes, their intersection creates a synergy that is revolutionising the way we think about digital ownership, creative monetisation, and decentralised finance.
The Role of NFTs in dApps
NFTs in dApps are redefining digital interactions. They’re not just about tokenizing digital art or collectibles; they’re also creating new paradigms in gaming, virtual real estate, and even in DeFi (Decentralised Finance). By representing unique digital and real-world assets, NFTs within dApps facilitate true ownership, transferability, and programmable features.
The Evolving Landscape of NFT dApps
NFT dApps are blockchain-based platforms enabling the creation, trading, and ownership of unique digital assets. This evolution is particularly visible in sectors like digital art, where platforms like OpenSea and Rarible have become hubs for artists to tokenize and sell their works as NFTs. In gaming, dApps like Decentraland utilise NFTs for in-game assets, fostering a thriving digital economy.
Creating and Launching an NFT dApp: A Step-by-Step Guide
- Conceptualisation: Begin by defining the NFT dApp’s purpose, target audience, and unique features.
- Blockchain Selection: Ethereum remains a popular choice for its robust support of NFT standards like ERC-721 and ERC-1155, although alternatives like BNB Smart Chain are also viable based on specific project needs.
- Development Environment: Set up your environment with necessary tools for smart contract development and testing.
- Smart Contract Development: Craft contracts to manage the NFTs’ lifecycle – minting, trading, and ownership transfer.
- Wallet Integration: Ensure users can securely manage their NFTs by integrating wallets like MetaMask or Trust Wallet.
- Minting Functionality: Develop user-friendly interfaces for creators to tokenize their assets.
- Unique and Decentralised Data Storage: Store your NFT data on a decentralised platform like Ethereum Swarm. This not only ensures true decentralisation of your NFTs but also enhances their security and accessibility.
- Marketplace Features: If your dApp includes trading functionalities, implement user-friendly buying, selling, and trading features.
- Testing and Deployment: Rigorously test your dApp for any vulnerabilities and deploy it to your chosen blockchain.
- Launch and Marketing: Craft a compelling narrative for your dApp, engage with influential community members, and utilise diverse platforms for promotion.
- Continual Development and Community Engagement: After launch, keep evolving the dApp based on user feedback and market trends to stay relevant and useful.
Solar Punk: Crafting the Future with Ethereum Swarm
At Solar Punk, our journey into the realm of NFT dApps is fuelled by our commitment to innovation and decentralisation. Building on Ethereum Swarm, we offer a unique proposition – a platform that not only supports decentralised applications but also enhances their efficiency, scalability, and security through decentralised data storage.
Our NFT dApps stand out for their resilience against network congestion and their ability to offer a seamless user experience, even amidst the growing complexity of blockchain transactions. By embracing Ethereum Swarm, Solar Punk is not just participating in the blockchain revolution; we are actively shaping its course, ensuring our NFT dApps are not just technologically superior but also aligned with the ethos of decentralised, user-centric innovation.
Closing Thoughts
As we continue to innovate and explore the vast potential of NFT dApps, we invite you to join us on this exciting journey. The future of digital ownership and creativity is here, and at Solar Punk, we are at the forefront, crafting solutions that redefine the digital landscape. If you’re interested in learning how we can help your project stand out with unique and innovative dApps, reach out to us here. Let’s build the future together.
Introducing the Access Control Trie (ACT) in Swarm
by András Arányi The Access Control Trie (ACT) is an essential feature designed to manage access control in Swarm’s decentralized storage infrastructure. It enables publishers to grant or revoke access to specific content at the chunk level using encrypted session keys. This guide will walk you through the key concepts…
Swarm Mobile: Web3 Power in Your Pocket
Discover Swarm Mobile, the new app bringing Web3 decentralized storage to Android. Learn how to run a Swarm Bee node and secure your digital sovereignty.
The Swarm File Manager: Bridging the Gap Between Web2 Comfort and Web3 Power
In our previous update, we introduced the concept of the Swarm File Manager: a radical layer of abstraction designed to make the unstoppable Swarm network as easy to use as a standard USB drive. Today, we are thrilled to announce that the vision is now a reality. The release of…
The Evolution of Streaming on Swarm: Introducing MSRS
Earlier this year, we took a significant step forward in decentralized multimedia with the release of our open-source multimedia libraries and the launch of the Multimedia Streaming Social Demo (MSSD). The MSSD was a proof of concept that demonstrated the power of live streaming on Swarm, showcasing a future free…
The Swarm File Manager: Bringing Cloud Storage Usability to Decentralized Storage
Swarm is the resilient, censorship-resistant, decentralized storage and communication layer of Web3. Its core strength lies in its layered design: the interwoven systems of Postage Stamps, Feeds, Chunking, and Incentives that ensure data persistence and integrity without reliance on any central server. However, complexity is the enemy of adoption. To…
From Universal Adapters to Decentralized Minds: The MCP Revolution
We should strive for a future where AI evolves not as a monolithic power in the hands of a few, but as a vibrant, decentralized ecosystem nurtured by many. We argued that this future is not only possible, but is actively being built on Swarm. That vision is no longer…
From IPFS to Swarm: Your Bridge to a Truly Decentralized Web
The path to a truly decentralized future often involves untangling ourselves from the lingering threads of centralized systems. At Solar Punk, we’re dedicated to forging the foundational infrastructure for censorship-resistant platforms and genuinely sovereign applications on Swarm. That’s why we’re thrilled to announce a major step forward for developers and…
The Future of AI is Decentralized, and It’s Being Built on Swarm
We stand at a crossroads. Artificial Intelligence is evolving at a breathtaking pace, but its immense power is becoming concentrated in the hands of a few giant corporations. This path leads to a future of data silos, central points of failure, and a world where we don’t truly own the…
Building the Unstoppable Web: Inspired by BitChat and the Power of Peer-to-Peer
The recent unveiling of Jack Dorsey’s BitChat is an exciting development in the quest for truly sovereign digital communication. Its core ethos of peer-to-peer, censorship-resistant messaging resonates deeply with our mission. While BitChat explores what’s possible using Bluetooth mesh networks, we at Solar Punk are building the tools for this…
The Price of Permanence: Comparing Swarm and Arweave
Storing data securely is essential for the decentralized internet. To meet this need, Arweave and Swarm both aim to provide a storage layer free from censorship, gatekeepers, and centralized control. Each system incentivizes node operators to store data reliably while keeping costs low enough to remain accessible, and high enough…
Unlocking True File Ownership: Swarm Desktop File Manager & Swarm Drive
In the ever-expanding universe of Web3, the dream of true digital sovereignty—where your data is undeniably yours, free from the clutches of centralized gatekeepers — is rapidly becoming a reality. At Solar Punk, we’re not just dreaming; we’re building the infrastructure that makes this future possible, facilitating applications of decentralized…
Tags
